How to Protect Identity from Complete Messages Operations Ore Re Audit
As an organization, faces numerous threats to its sensitive information, including identity theft, data breaches, and fraud. Sensitive personal information, such as names, social security numbers, credit card numbers, and other account data, is widely used in business operations. However, a security audit is a process of identifying, evaluating, and resolving vulnerabilities in an organization's security posture to ensure compliance with information security audit requirements.Why is a Security Audit Important?
A security audit is essential to understand how it affects the management of sensitive information and compliance with information security auditor requirements. By conducting regular security audits, an organization can: * Identify vulnerabilities and weaknesses in its security posture * Develop strategies to mitigate potential risks * Comply with regulatory and compliance requirements * Protect sensitive information from unauthorized access * Ensure the overall security and integrity of the organization's operations8 Checklist Points to Strengthen Your IAM Strategy
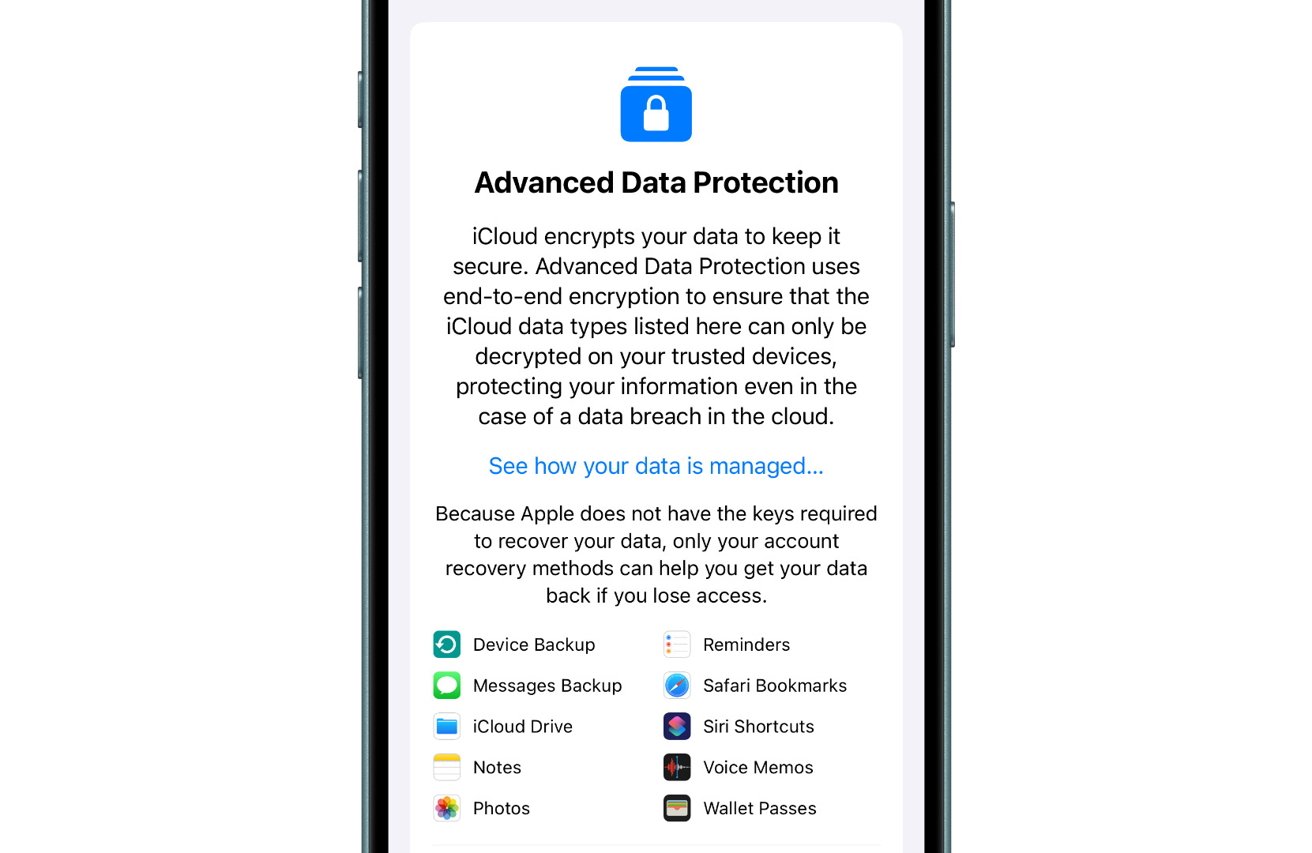
To strengthen your Identity and Access Management (IAM) strategy, follow these 8 checklist points to ensure compliance with IAM audit requirements for a secure and efficient identity management system: 1. **Assess Your Current IAM Infrastructure**: Evaluate your current IAM infrastructure to identify areas for improvement. 2. **Implement Multi-Factor Authentication**: Implement multi-factor authentication to provide an additional layer of security. 3. **Use Identity Analytics**: Use identity analytics to identify and analyze security risks and anomalies. 4. **Implement Access Reviews**: Regularly review and update user access to sensitive information and resources. 5. **Use Identity Governance**: Implement identity governance to ensure consistent access controls and monitoring. 6. **Monitor and Respond to Security Incidents**: Monitor for security incidents and respond promptly to minimize damage. 7. **Continuously Test and Update**: Continuously test and update your IAM infrastructure to stay ahead of emerging threats. 8. **Conduct Regular Security Audits**: Conduct regular security audits to ensure compliance with IAM audit requirements.Understanding the Role of Audits in Cybersecurity