Protecting Data From Ransomware Infections: A Comprehensive Guide
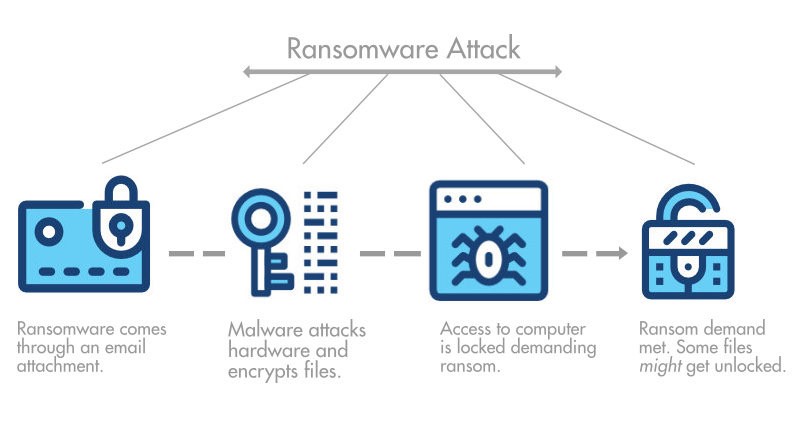
Ransomware, a type of malware that encrypts a user's or organization's most important files or data, has been a persistent threat in the world of computer security for many years. These destructive, financially-motivated attacks, where cybercriminals demand payment to decrypt data and restore access, can severely impact business processes and leave organizations without the data they need to operate and deliver mission-critical services.
What is Ransomware?
Protecting Against Malicious Code for more information on malware.) After the initial infection, ransomware will attempt to spread to connected systems, including shared storage drives and other accessible computers.
Understanding the Risks of Ransomware Infections
When ransomware strikes, your organization needs to learn of an infection and investigate quickly so that you can protect your systems and data. Most organizations struggle to contain incidents quickly, however. In its 2023 Cost of a Data Breach Report, IBM found that organizations took 204 days to identify a breach and 73 days to contain them.
Protecting Against Ransomware Infections
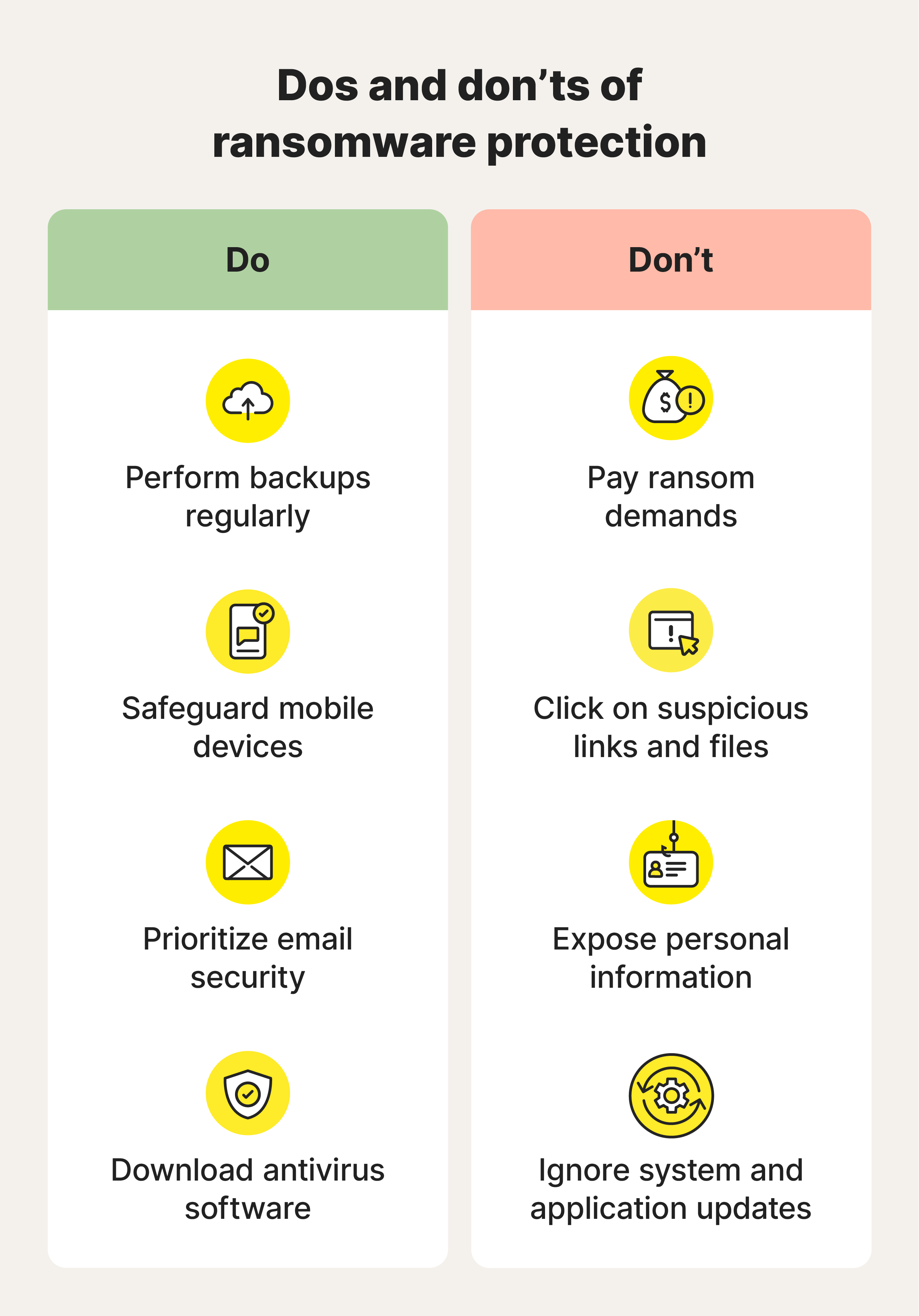
Protecting against ransomware infections requires a multi-layered approach that encompasses both technological measures and behavioral adjustments. By understanding the avenues through which ransomware can infiltrate devices, individuals and organizations can better shield themselves against such threats. Implementing a robust backup plan and regular software updates, for instance, are crucial steps towards ransonware prevention.
Prevention Strategies
- Back up data regularly. Create backup copies of files and store them on removable media or in online storage to protect your information from malware and computer damage.
- Update software regularly. Use security software that can detect and remove malware and viruses. Update your software regularly, or set it to update automatically, for the most up-to-date protection.
- Use strong passwords. Ransomware attacks often involve stolen credentials. LastPass removes this vulnerability by generating and storing strong, unique passwords for every account your team uses.

Response Strategies
- Employ a data backup and recovery plan. This can help minimize the impact of a ransomware attack by providing access to backed-up data.
- Gain system access. If your organization is subject to a ransomware attack, make sure you have system access to prevent further malware propagation.
- Use ransomware-specific solutions. Fortra's data loss prevention (DLP) software can help protect data across endpoints, cloud, and SaaS apps.
Using the Joint CISA and MS-ISAC Ransomware Guide
The Cybersecurity and Infrastructure Security Agency (CISA) strongly recommends responding to ransomware by using the Joint CISA and Multi-State Information Sharing and Analysis Center (MS-ISAC) Ransomware Guide. This information will take you through the response process from detection to containment and eradication, providing a structured and effective way to address ransomware attacks.
Key Ransomware Protection Strategies
- Regular updates and patches. Regularly update your software to ensure that any discovered vulnerabilities are prevented.
- Safe backup and archival. Maintain safe backup and archival methods to prevent malicious software attacks from tampering with your files.
- Enhanced protocols. Consider engaging a subclass of cybersecurity solution, known as a "endpoint protection" solution, to flesh out your existing network defenses with encapsulated, quarantine-holding endpoint scanning technology.
Protecting data from ransomware infections requires comprehensive and ongoing efforts. Implementing these measures can help prevent, detect, and contain ransomware attacks. Regularly developing and maintaining your organization's cybersecurity program, and staying informed about emerging threats and risks, is crucial for ensuring business continuity and minimizing potential financial and reputational impacts of a ransomware incident.
Conclusion
Ransomware is a destructive and financially-motivated malware attack that can have severe impacts on a business or organization. Protecting against ransomware infections requires a comprehensive approach that includes technical measures, behavioral adjustments, and regular maintenance of cybersecurity software and systems. By following the guidelines and strategies outlined in this guide, organizations can better shield themselves against such threats, thereby safeguarding their data and preventing unplanned financial and reputational impacts due to cyberattacks.