Secure Online Data Protection Techniques: Protect Your Digital Assets
In today's digital age, protecting your online data is more crucial than ever. With the rise of cyber threats and data breaches, it's essential to implement robust secure online data protection techniques to safeguard your sensitive information. In this article, we'll explore the various methods and technologies that can help you protect your digital assets and maintain your online privacy.
Understanding Data Protection
Data protection is a set of strategies and processes that aim to secure the privacy, availability, and integrity of your data. It involves a comprehensive approach that includes encryption, secure authentication, access control, network security, and physical security. By implementing effective data protection measures, you can prevent unauthorized access, data breaches, and reputational harm.
Secure Data Protection Techniques
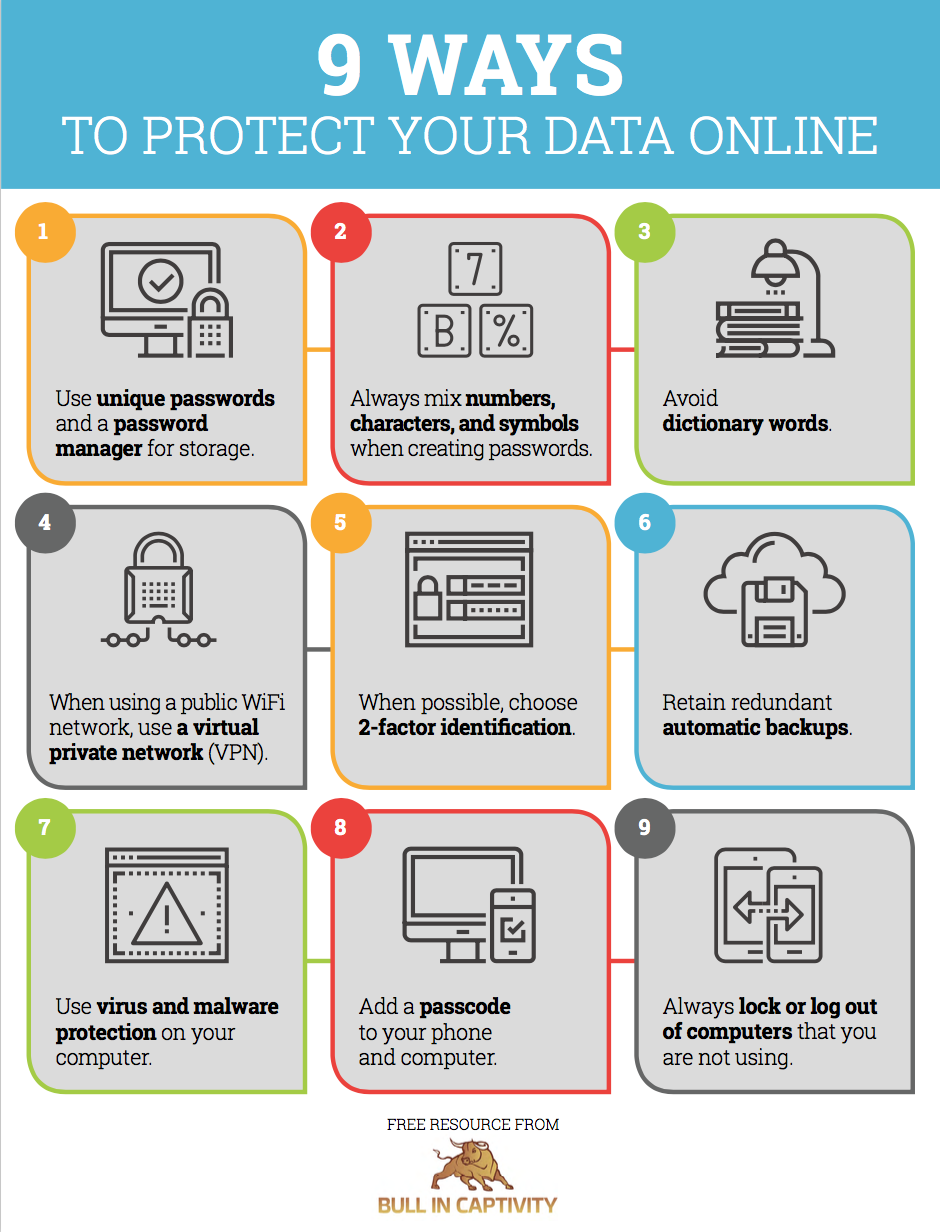
Here are some essential secure online data protection techniques that you can implement:
- Encryption**: Transforming data into a code to prevent unauthorized access. There are different types of encryption, including symmetric, asymmetric, and hybrid encryption.
- Access Control**: Regulating who can access your data and what actions they can perform. Implementing role-based access control and multi-factor authentication can add an extra layer of security.
- Secure Communication**: Using secure communication protocols like HTTPS and SFTP to encrypt data in transit.
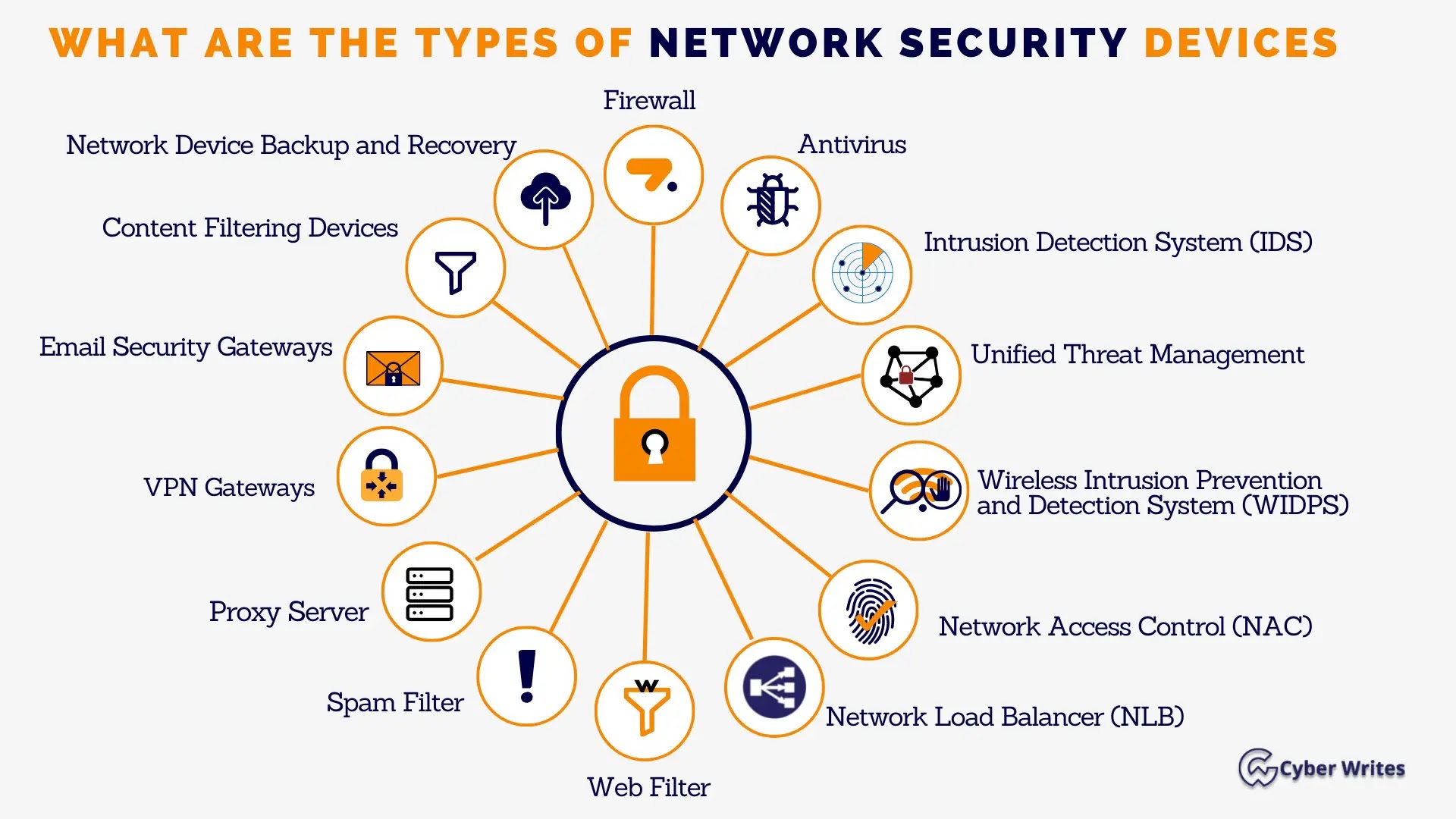
- Network Security**: Implementing firewalls, intrusion detection systems, and virtual private networks (VPNs) to prevent unauthorized access to your network.
- Physical Security**: Protecting your physical assets, such as servers and storage devices, with secure housing, access controls, and surveillance systems.
- Data Anonymization**: Making your data anonymous to prevent linking it back to your identity.
- Tokenization**: Replacing sensitive data with tokens to prevent unauthorized access.
- Secure Authentication**: Using multi-factor authentication, biometric authentication, and other secure authentication techniques to verify user identities.
- Regular Updates and Backups**: Regularly updating your software and systems and backing up your data to prevent data loss and ensure business continuity.

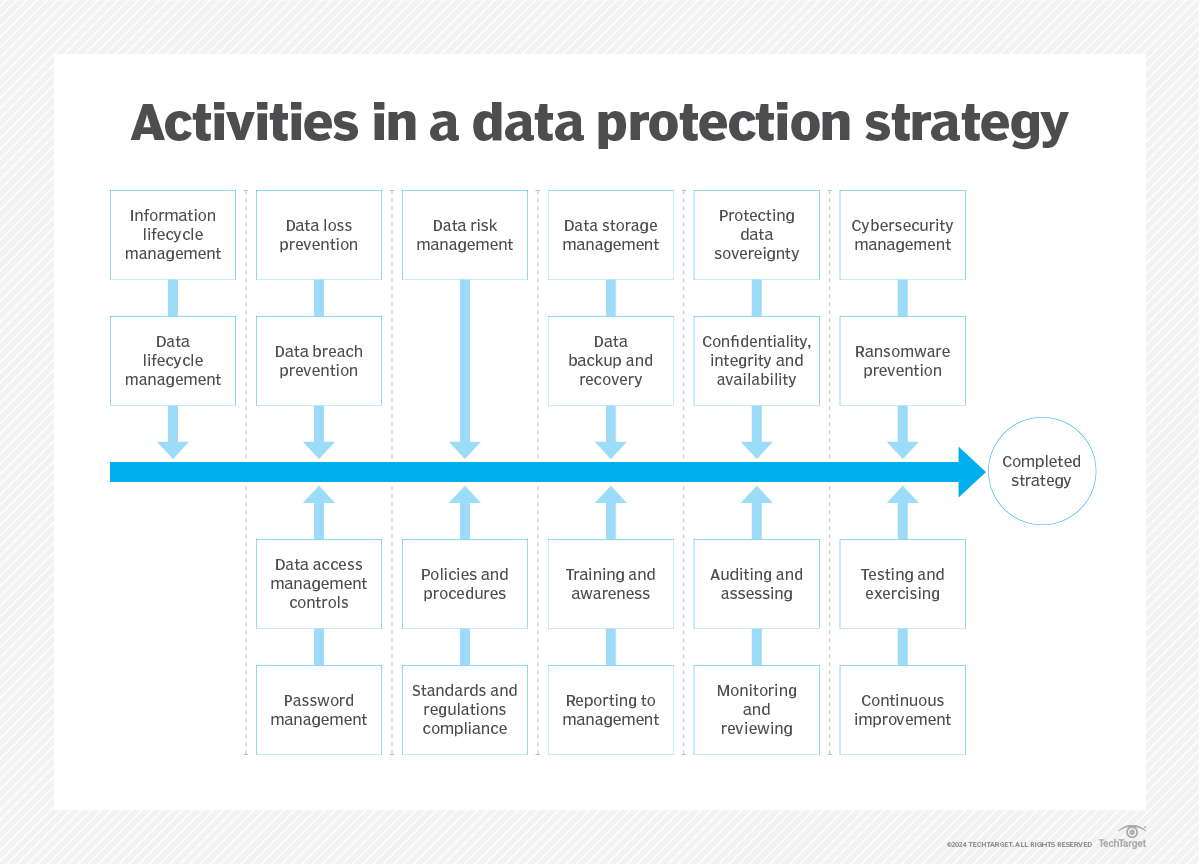
Implementing Secure Data Protection Techniques
Implementing secure online data protection techniques requires a comprehensive approach that involves people, processes, and technology. Here are some steps you can follow:
- Conduct a Risk Assessment**: Identify potential vulnerabilities and threats to your data and systems.
- Develop a Data Protection Policy**: Establish a clear policy that outlines your data protection responsibilities and procedures.
- Implement Secure Technologies**: Choose secure technologies that meet your data protection needs, such as encryption software and secure authentication solutions.
- Train Your Staff**: Educate your staff on data protection best practices and ensure they understand their roles and responsibilities.
- Regularly Update and Test**: Regularly update and test your systems and processes to ensure they remain secure and effective.
Conclusion
Secure online data protection techniques are essential for protecting your digital assets and maintaining your online privacy. By implementing a comprehensive approach that includes encryption, access control, secure communication, network security, physical security, data anonymization, tokenization, and secure authentication, you can prevent unauthorized access, data breaches, and reputational harm. Remember to regularly update and test your systems and processes to ensure they remain secure and effective.