How to Protect Yourself from Online Exploitation
In today's digital age, the internet has become an integral part of our lives. We use it for communication, entertainment, education, and many other purposes. However, with the increasing use of the internet, there are also risks associated with it. One of the most significant risks is online exploitation, which can have severe consequences on individuals and families.
Understanding Online Exploitation
Online exploitation refers to the use of technology to exploit or harm individuals, often for financial or personal gain. This can include a range of activities such as identity theft, cyberbullying, sextortion, and online harassment. Online exploitation can occur through various means, including social media, online forums, and messaging apps.
Risks of Online Exploitation
The risks of online exploitation are numerous, and can have severe consequences on individuals and families. Some of the risks include:
- Identity theft and financial loss
- Cyberbullying and online harassment
- Sextortion and online exploitation
- Unwanted exposure to explicit content
- Emotional distress and mental health issues
How to Protect Yourself from Online Exploitation
Fortunately, there are steps you can take to protect yourself and your loved ones from online exploitation. Here are some tips to help you stay safe online:
1. Be Cautious with Personal Information
When sharing personal information online, be cautious and limit the amount of information you share. Avoid sharing sensitive information such as your address, phone number, or financial information.
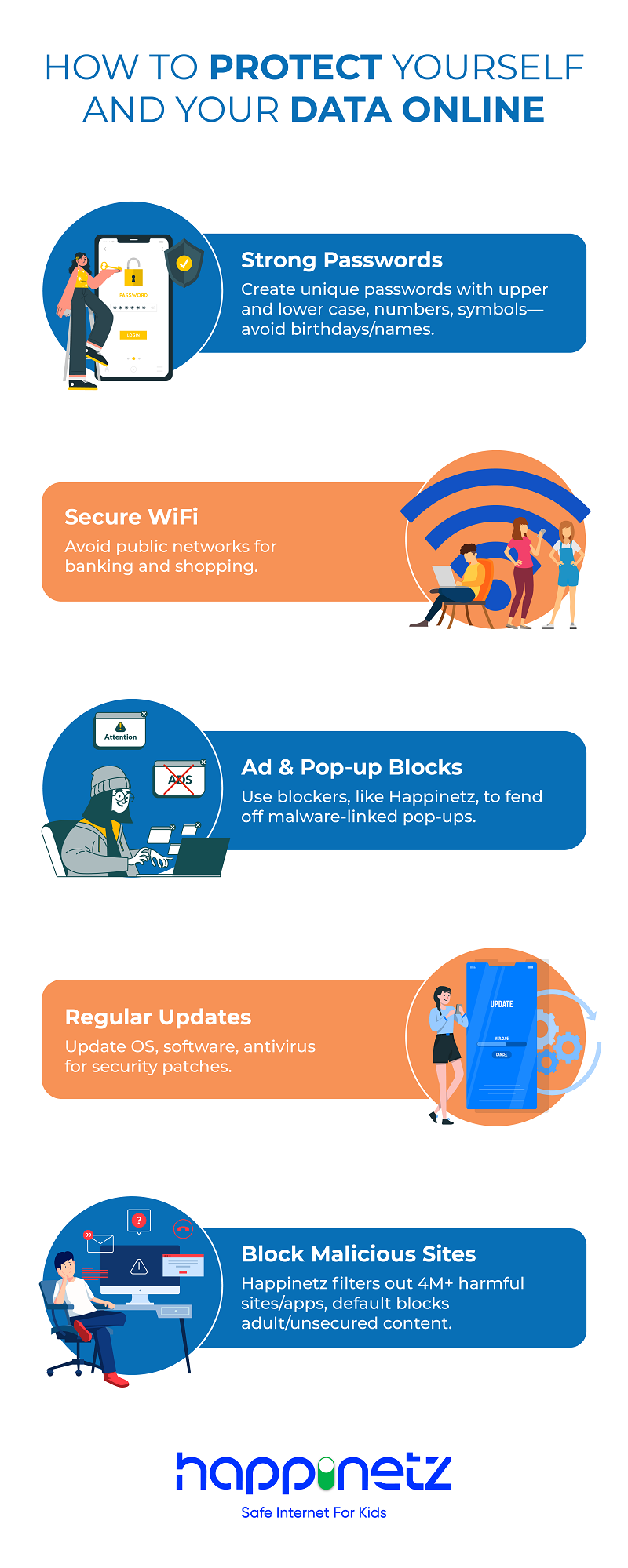
2. Use Strong Passwords and Enable Two-Factor Authentication
Use strong and unique passwords for each of your online accounts, and enable two-factor authentication (2FA) whenever possible. This will help prevent unauthorized access to your accounts.
3. Monitor Your Online Activity
Regularly monitor your online activity, including your social media accounts, email, and messaging apps. Report any suspicious activity to the relevant authorities.

4. Use Secure Browsers and Extensions
Use secure browsers and extensions that can help protect you from online threats. Some popular options include Tor, VPNs, and anti-virus software.
5. Report Suspicious Activity
Report any suspicious activity to the relevant authorities, including law enforcement and online platforms.
6. Educate Yourself and Others
Stay informed about online safety and exploitation, and educate yourself and others about the risks and prevention strategies.
Conclusion
Online exploitation is a serious issue that can have severe consequences on individuals and families. By taking the necessary precautions and staying informed, you can protect yourself and your loved ones from online exploitation. Remember, online safety is a shared responsibility, and we must all work together to prevent exploitation and keep our online communities safe.
Resources
For more information on online safety and exploitation, check out the following resources:
- StopCyberbullying.gov
- Cybercrime.gov
- Privacy Rights Clearinghouse
- ONLINEaccess
Take Action
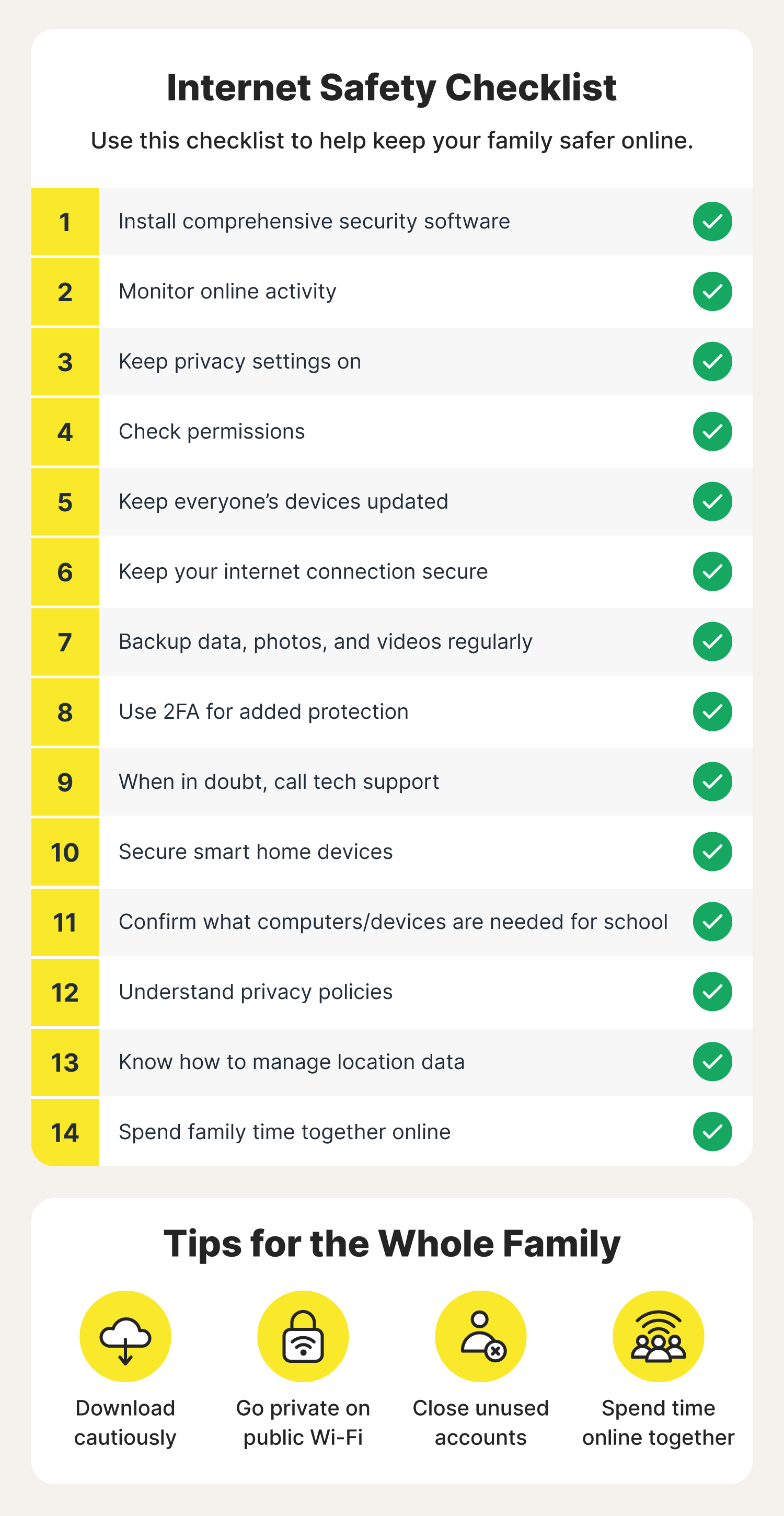
Take the following steps to protect yourself from online exploitation:
- Review your online accounts and passwords
- Enable two-factor authentication
- Monitor your online activity
- Report suspicious activity
- Stay informed and educated