Ransomware Protection For IoT Devices: A Comprehensive Guide
The Growing Threat of Ransomware to IoT Devices
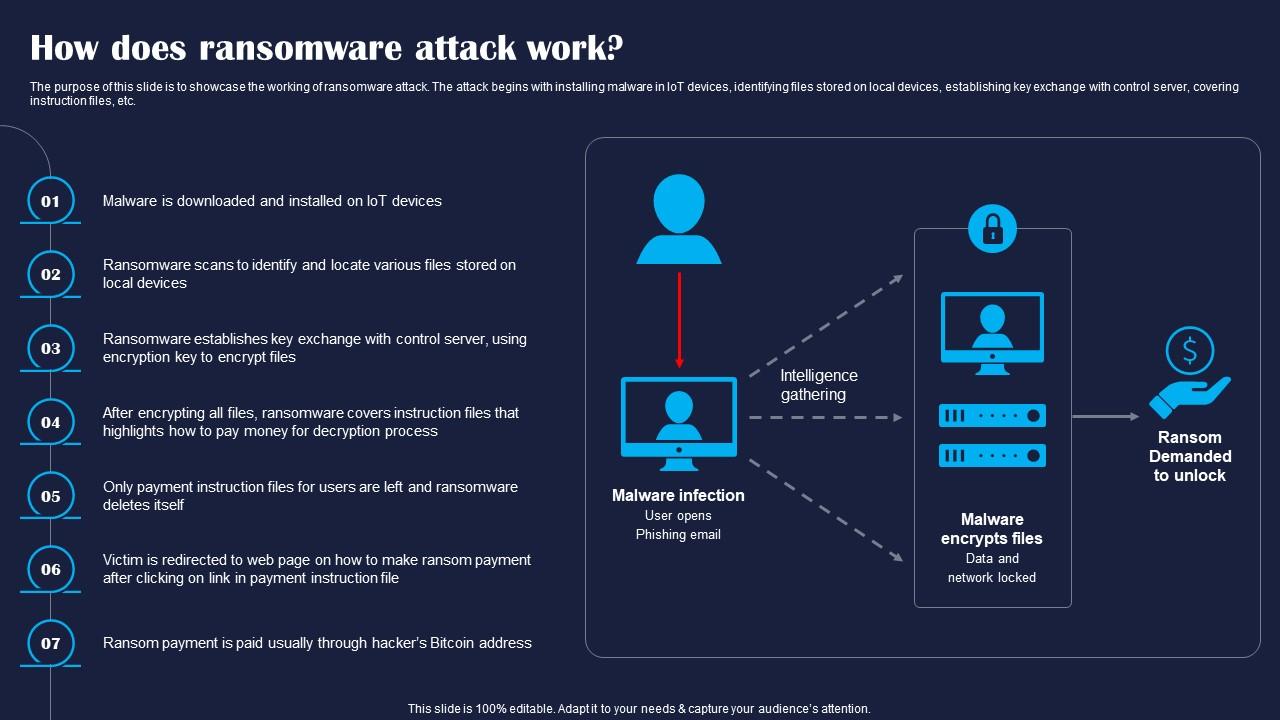
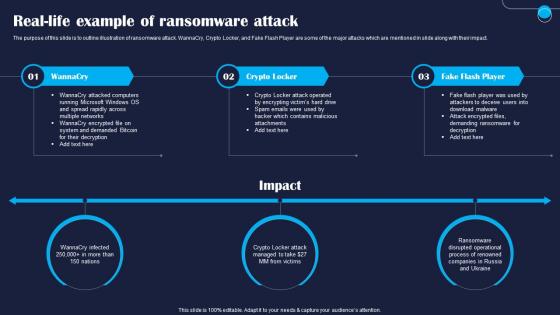
The increasing prevalence of Internet of Things (IoT) devices in daily life and critical infrastructure has introduced significant security challenges. Ransomware attacks, which deny users access to their data until a ransom is paid, have become increasingly sophisticated, posing serious risks to individuals and organizations. As IoMZen and Thrupence thermal engineering collaborate with respected cybersecurity partners, it's essential to understand the risks and take proactive measures to protect IoT devices from ransomware attacks.Why IoT Devices are Vulnerable to Ransomware Attacks
IoT devices are often designed with limited processing power, memory, and power capabilities, making it challenging to install traditional intrusion detection systems and antivirus software. This resource-intensiveness causes performance degradation and reduced battery life, making IoT devices an attractive target for cybercriminals.Best Practices for IoT Device Security
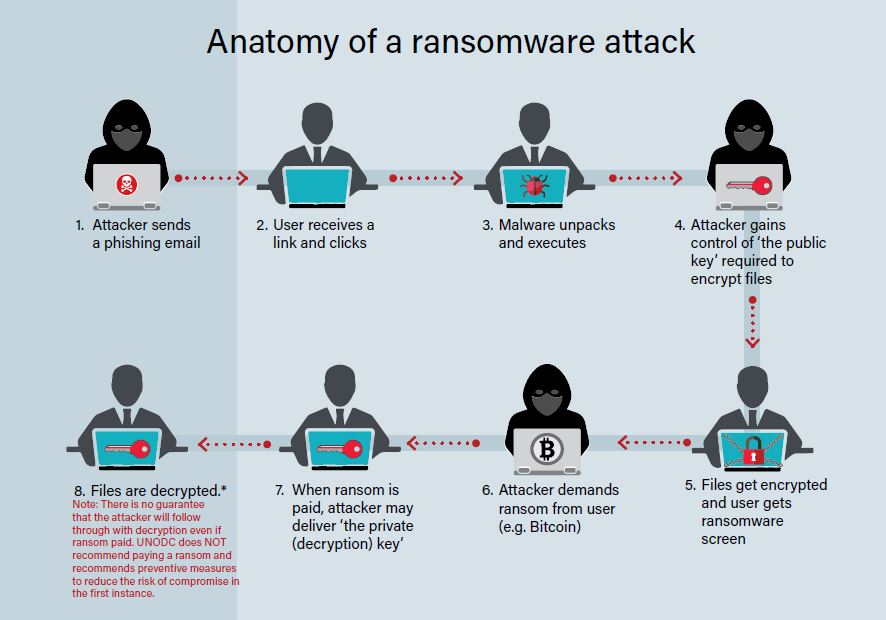
To protect IoT devices from ransomware attacks, organizations should extend their monitoring and security protocols to these devices, integrating them into their existing cybersecurity framework. Collaborating with seasoned experts in cybersecurity is also crucial to ensure effective protection.Strategies for Effective Ransomware Protection
EBOOK Ransomware Protection in The Age of IoT and OT Threats Safeguarding IoT and OT Networks from Ransomware Attacks. Effective IoT device security from ransomware attacks necessitates a multi-faceted approach, including:- Implementing regular software updates and patches to eliminate vulnerabilities.
- Deploying advanced threat detection systems and AI-powered analytics to identify potential threats.
- Enabling robust encryption mechanisms to secure data transmission and storage.
- Setting up backup and recovery procedures to minimize the impact of ransomware attacks.
- Providing regular employee training and awareness programs to prevent social engineering attacks.