Wireless Network Security Compliance: Protecting Your Network from the Risks
Understanding the Importance of Wireless Network Security Compliance
As organizations increasingly rely on wireless networks to connect their devices and employees, the importance of wireless network security compliance has become a top priority. Wireless networks are a critical component of modern business operations, but they also pose a significant risk to an organization's security and compliance. In this article, we will delve into the world of wireless network security compliance, discussing the key threats, best practices, and regulatory requirements that organizations must follow to protect their networks.The Wireless Attack Surface
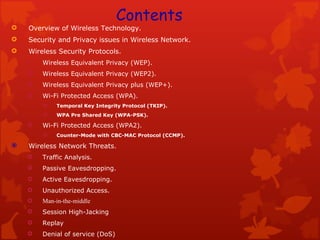
Wireless networks propagate beyond the physical constraints of the wired network, increasing the attack surface for cyber attacks. There are several types of wireless threats that organizations must be aware of, including:- Passive scanning attacks: These occur when malicious entities scan the network for vulnerabilities.
- Layer 2 active spoofing attacks: These attacks involve masquerading as a legitimate device on the network.
- Layer 1 active jamming or DoS attacks: These attacks involve disrupting the network by transmitting a strong signal or flooding the network with traffic.
The Consequences of Non-Compliance
Failing to maintain wireless network security compliance can have severe consequences, including:- Unauthorized access to sensitive data: Wireless networks can expose sensitive data to unauthorized access, leading to data breaches and non-compliance with regulatory requirements.
- Compromised intellectual property: Wireless networks can be exploited to steal sensitive intellectual property, leading to significant losses for organizations.
- Reputational damage: A security breach can damage an organization's reputation, making it difficult to recover and regain customer trust.

Best Practices for Wireless Network Security Compliance
To maintain wireless network security compliance, organizations must adhere to the following best practices:- Implement robust security protocols: Organizations must implement robust security protocols, including WPA2 or WPA3 encryption, to secure wireless traffic.
- Conduct regular security audits: Regular security audits can help identify vulnerabilities and ensure that the network is secure.
- Implement access controls: Implementing access controls, such as passwords and authentication protocols, can prevent unauthorized access to the network.
- Monitor network traffic: Monitoring network traffic can help identify potential security threats and prevent attacks.
Regulatory Requirements
Organizations must comply with regulatory requirements to ensure wireless network security compliance. Some of the key regulatory requirements include:- ISO 27001: This international standard provides a framework for information security management systems.
- SOC 2: This standard provides a framework for service organizations to demonstrate their commitment to security and compliance.
- NIST 800-53: This standard provides a framework for managing and mitigating physical and technical risks to information systems.
- CMMC 2.0: This standard requires organizations to protect wireless access using strong authentication and encryption.