Data Encryption Methods for Protection: A Comprehensive Guide
In today's digital landscape, data breaches and cyber threats continue to rise at an alarming rate. With the increasing number of data breaches, it has become essential for organizations to implement robust encryption methods to protect sensitive data. In this article, we will discuss various data encryption methods for protection, including symmetric and asymmetric encryption, common algorithms, and best practices.
What is Data Encryption?
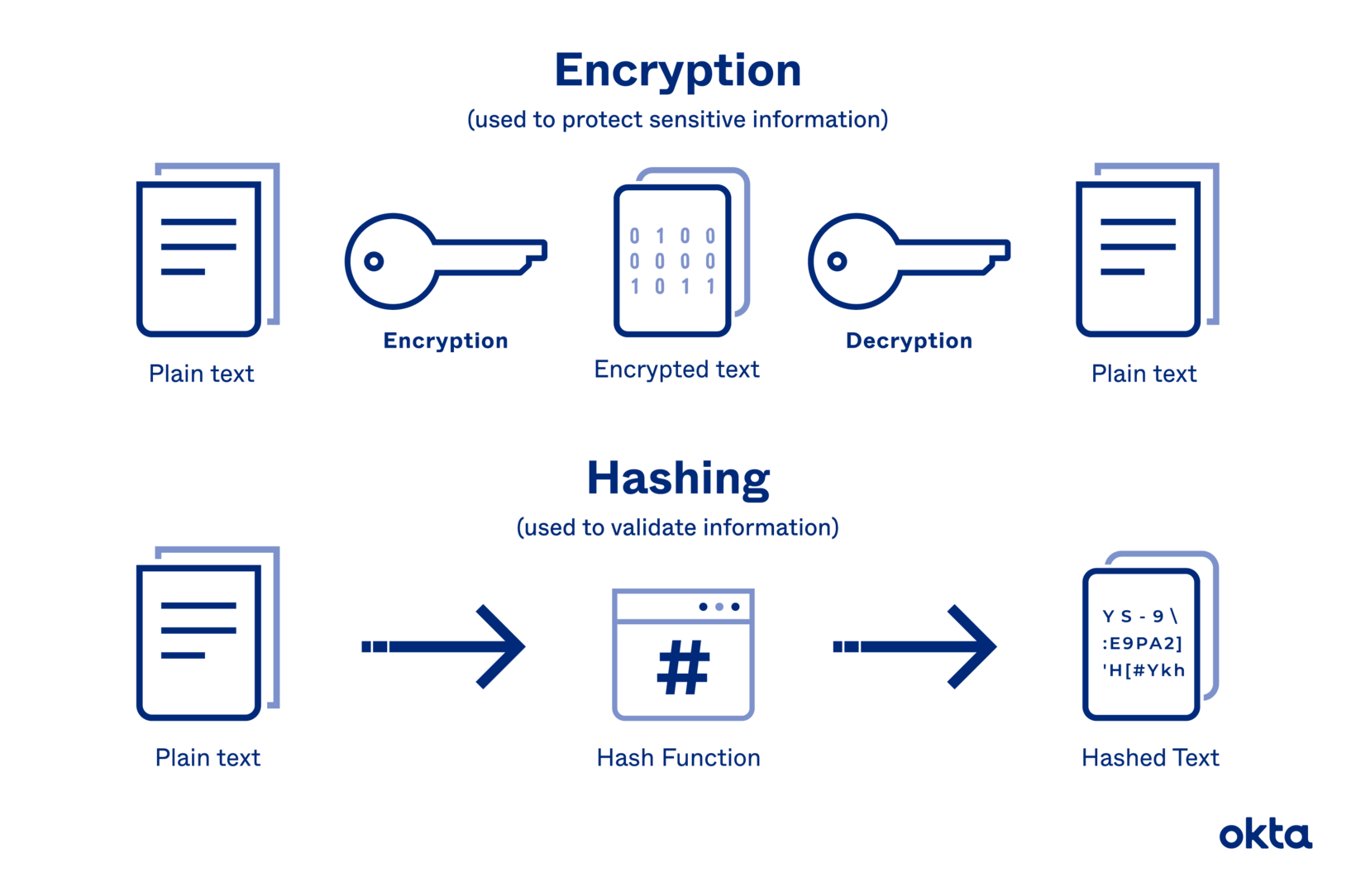
Data encryption is a security method that translates data into a code, or ciphertext, that can only be read by people with access to a secret key or password. This process protects data from being stolen, changed, or compromised. There are two main types of encryption: symmetric and asymmetric.
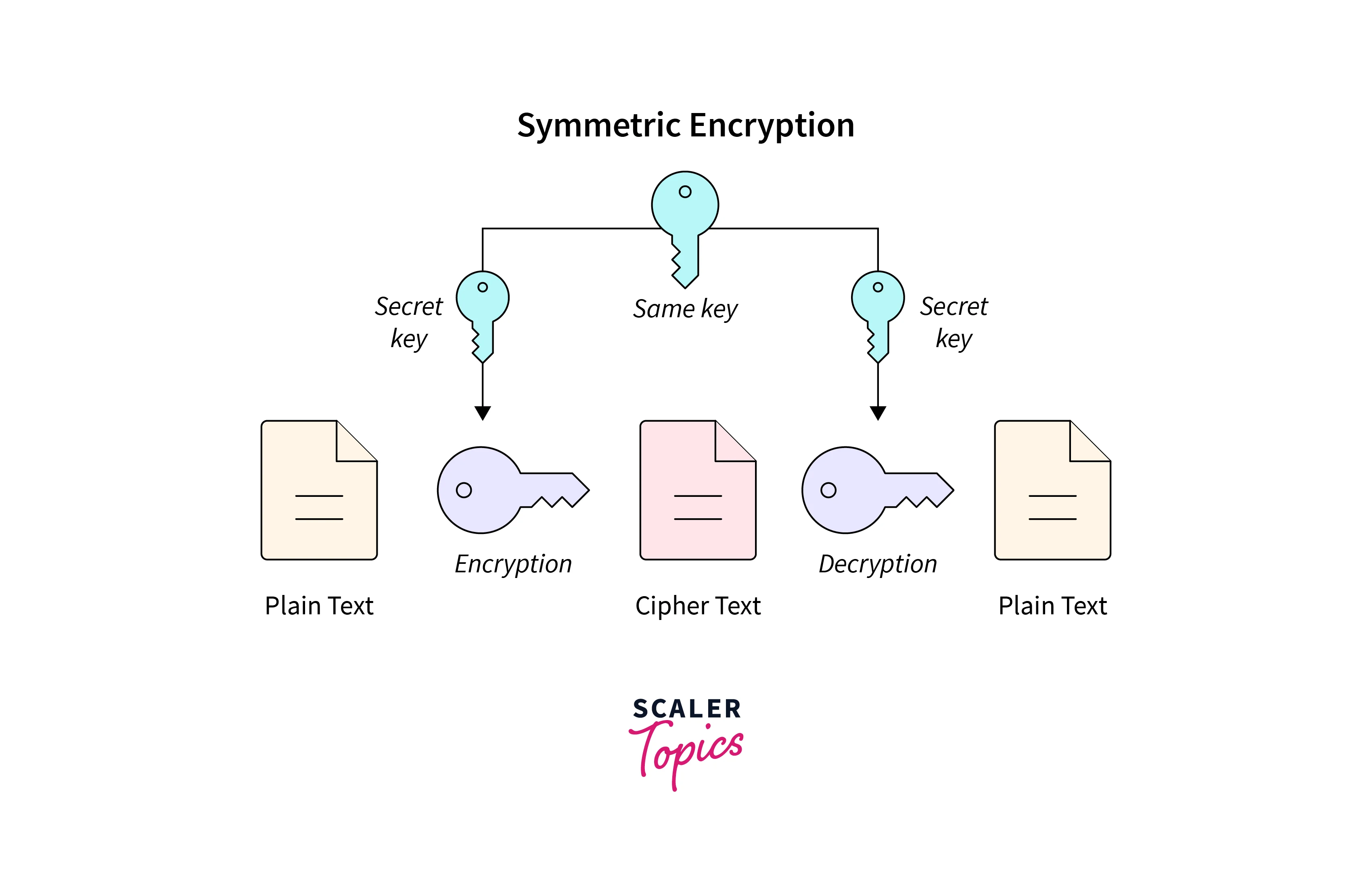
Symmetric Encryption
Symmetric encryption uses a single key for both encryption and decryption. It's efficient for large data volumes, but it requires the same key to be shared among all users. If the key is compromised, the entire system is vulnerable.
Asymmetric Encryption
Asymmetric encryption uses a pair of keys: a public key for encryption and a private key for decryption. This method is more secure than symmetric encryption, as the public key can be shared freely without compromising the system's security.
Common Encryption Algorithms
There are several common encryption algorithms used today, including:
- AES (Advanced Encryption Standard): A widely used symmetric-key block cipher that provides strong encryption.
- RSA (Rivest-Shamir-Adleman): A widely used asymmetric-key encryption algorithm that provides secure key exchange and digital signatures.
- SHA-256 (Secure Hash Algorithm 256): A cryptographic hash function that provides data integrity and authenticity.
Best Practices for Data Encryption
To implement effective data encryption, follow these best practices:
- Use strong encryption algorithms: Choose algorithms that are widely accepted and have a proven track record of security.
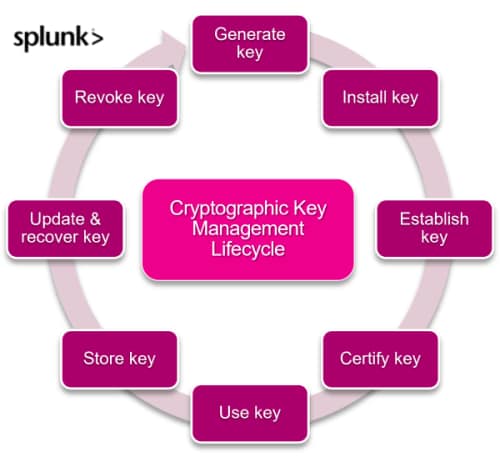
- Use key management systems: Implement key management systems to securely generate, distribute, and manage encryption keys.
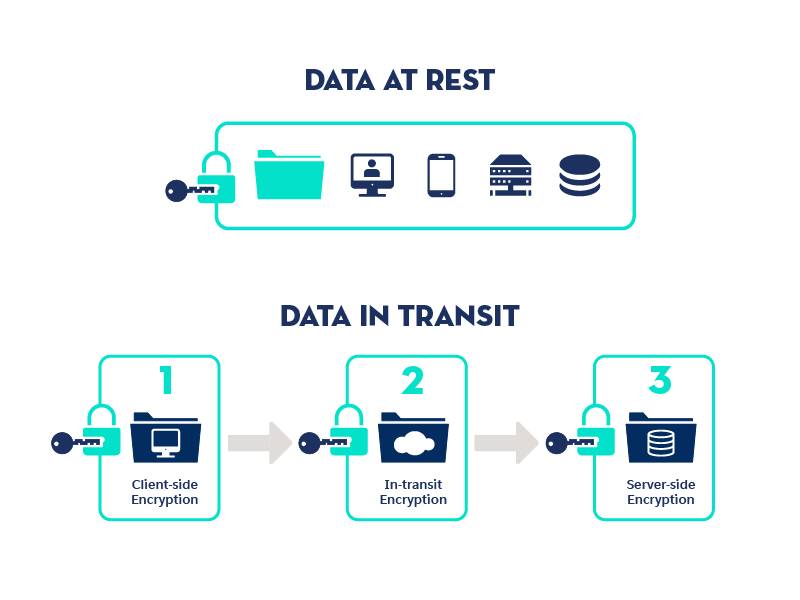
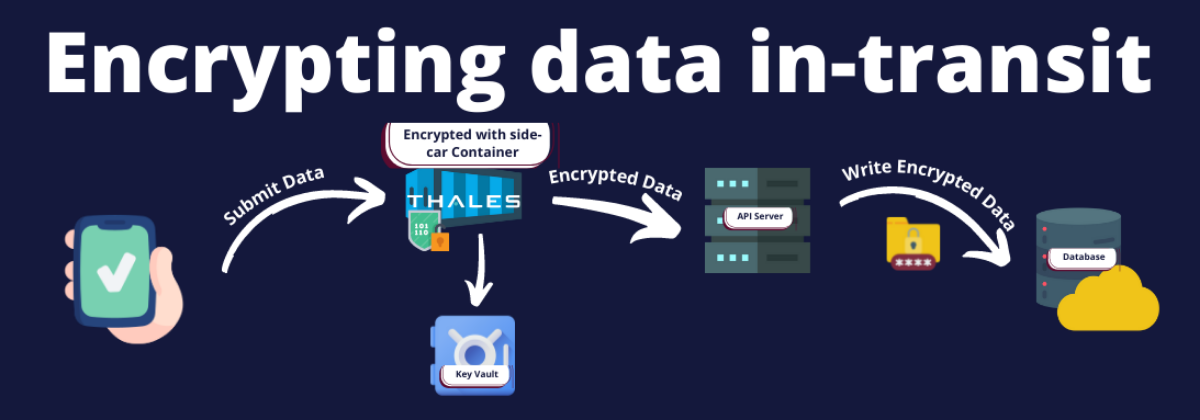
- Use secure communication channels: Use secure communication channels, such as SSL/TLS, to protect data in transit.
- Regularly update and patch encryption software: Regularly update and patch encryption software to ensure you have the latest security patches.
Conclusion
Implementing robust data encryption methods is crucial for protecting sensitive data in today's digital landscape. By understanding the different types of encryption, common algorithms, and best practices, organizations can ensure the security and integrity of their data. Remember to use strong encryption algorithms, key management systems, secure communication channels, and regularly update and patch encryption software to protect your data from unauthorized access.