Strengthen Your Business Security with Data Protection Techniques
In today's digital landscape, data protection is no longer a choice but a necessity for businesses of all sizes. With the increasing sophistication of cyber threats and the growing importance of data in business operations, it's essential to have robust data protection techniques in place. In this article, we'll explore the key components, best practices, and essential technologies that can help you build a resilient data protection strategy.
What is Data Protection?
Data protection is the process of safeguarding sensitive information from damage, loss, or corruption. It involves a set of strategies and processes designed to protect the privacy, availability, and integrity of data. A robust data protection strategy is vital for any organization that collects, stores, and processes sensitive data.
Importance of Data Protection Techniques
Effective data protection techniques can help your business in several ways:
- Prevent data breaches and reputational harm
- Avoid financial losses due to unauthorized access or data damage
- Improve your business's overall security posture
- Meet regulatory requirements and compliance standards
- Protect sensitive customer and business data
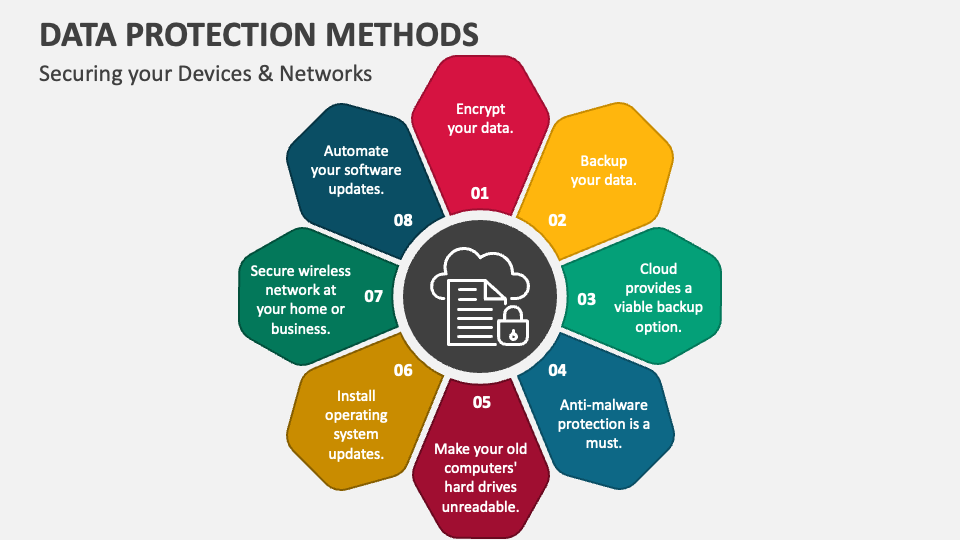
Key Components of a Robust Data Protection Strategy
A comprehensive data protection strategy should include the following key components:
- Full visibility into what data your organization relies on, where it is stored, and who can access it
- Consistent enforcement of data monitoring protocols and employee training
- Regular security audits and risk assessments
- Implementation of data encryption technologies
- Access controls and user authentication
- Continuous data backup and recovery strategies
- Data loss prevention (DLP) technologies
- Endpoint security and endpoint detection and response (EDR)
Best Practices for Data Protection
To build a robust data protection strategy, follow these best practices:
- Implement a data classification program to categorize and protect sensitive data
- Use encryption technologies to protect data in transit and at rest
- Enforce multi-factor authentication (MFA) for all users and devices
- Use access controls and user authentication to limit access to sensitive data
- Regularly back up and recover data to ensure business continuity
- Implement DLP technologies to monitor and protect sensitive data
- Use EDR technologies to detect and respond to endpoint threats
- Conduct regular security audits and risk assessments
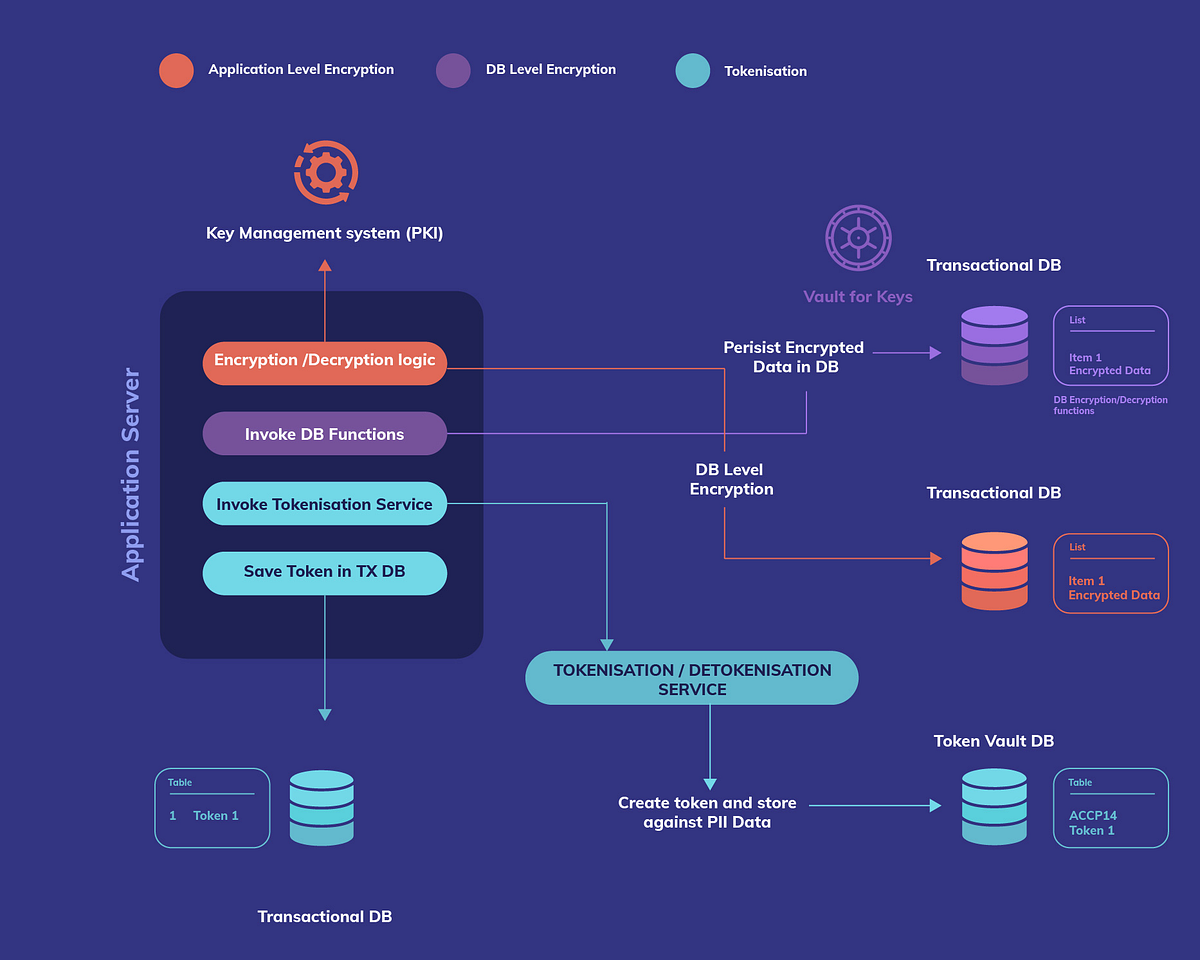
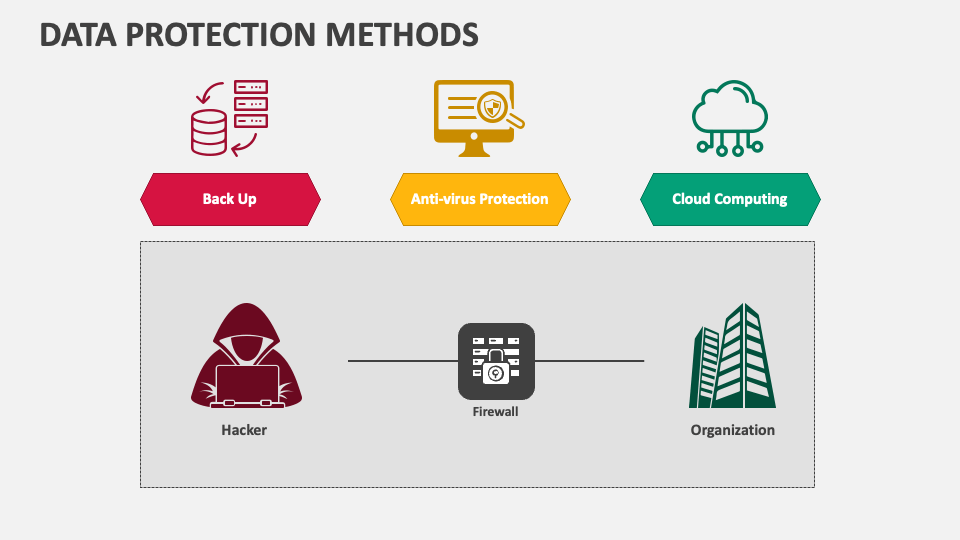
Essential Data Protection Technologies
There are several essential data protection technologies that you should consider implementing:
- Encryption technologies (e.g., AES, PGP)
- DLP technologies (e.g., Filesystem, Database)
- Access controls and user authentication (e.g., Identity Access Management, Single Sign-On)
- Endpoint security and EDR technologies (e.g., antivirus, intrusion detection systems)
- Backup and recovery technologies (e.g., Snapshot, Continuous Backup)
- Cloud-based security services (e.g., cloud-based DLP, cloud-based access controls)
Conclusion
Strengthening your business security with data protection techniques involves understanding the importance of data protection, implementing a robust data protection strategy, and following best practices. By using the key components, essential technologies, and best practices outlined in this article, you can help prevent data breaches, reputational harm, and financial losses, and ensure business continuity in today's ever-evolving digital landscape.