Protect Your Online Data: Understanding the Importance of Online Encryption Methods
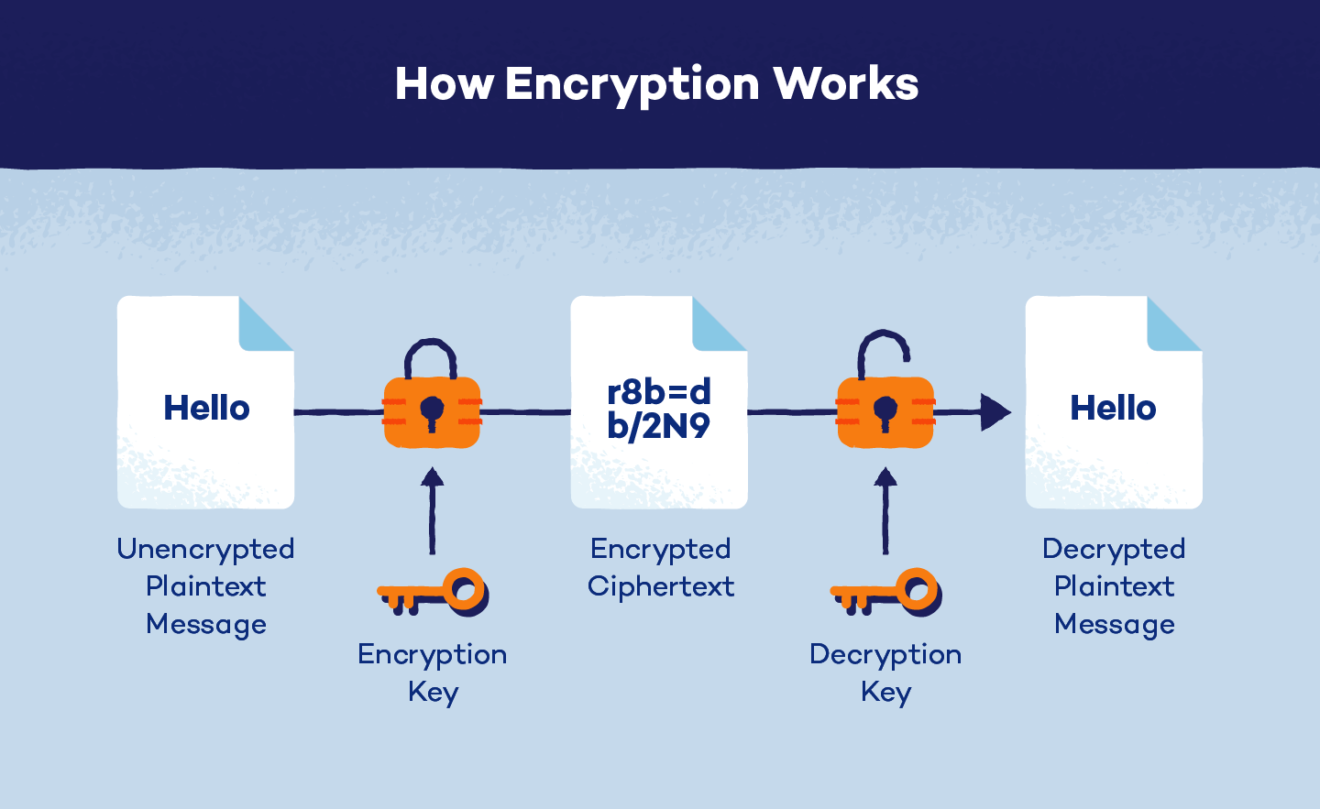
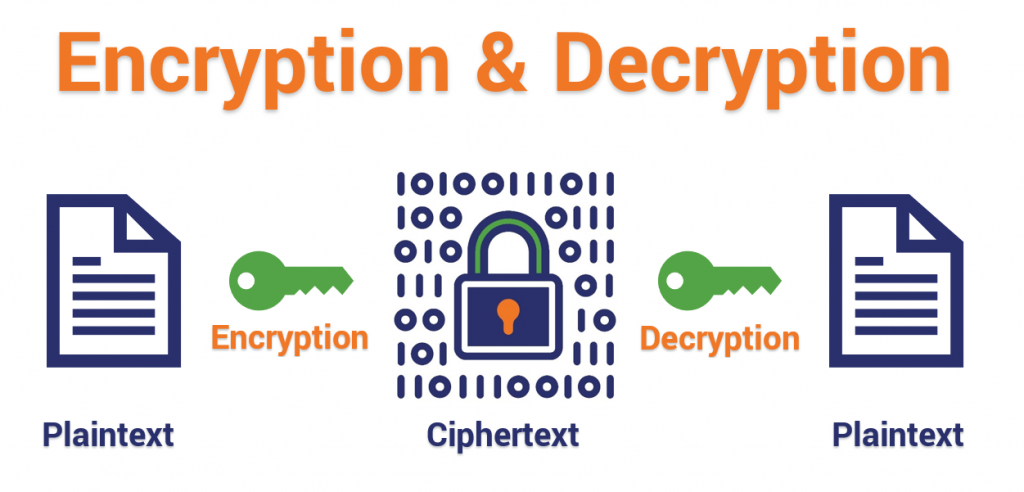
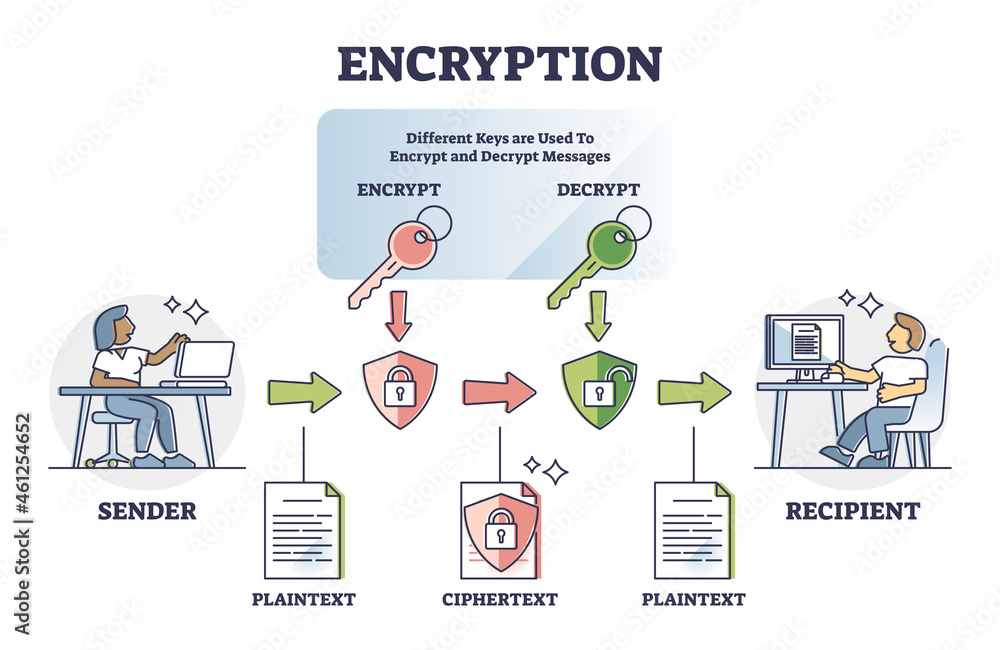
In today's digital age, cybersecurity is a top priority for individuals and organizations alike. One of the most effective ways to protect sensitive information is through online encryption methods. Encryption is the process of scrambling data to make it unreadable to unauthorized individuals, and there are various methods and algorithms used to achieve this. In this article, we will delve into the world of online encryption methods, exploring their types, uses, and benefits.
Types of Online Encryption Methods
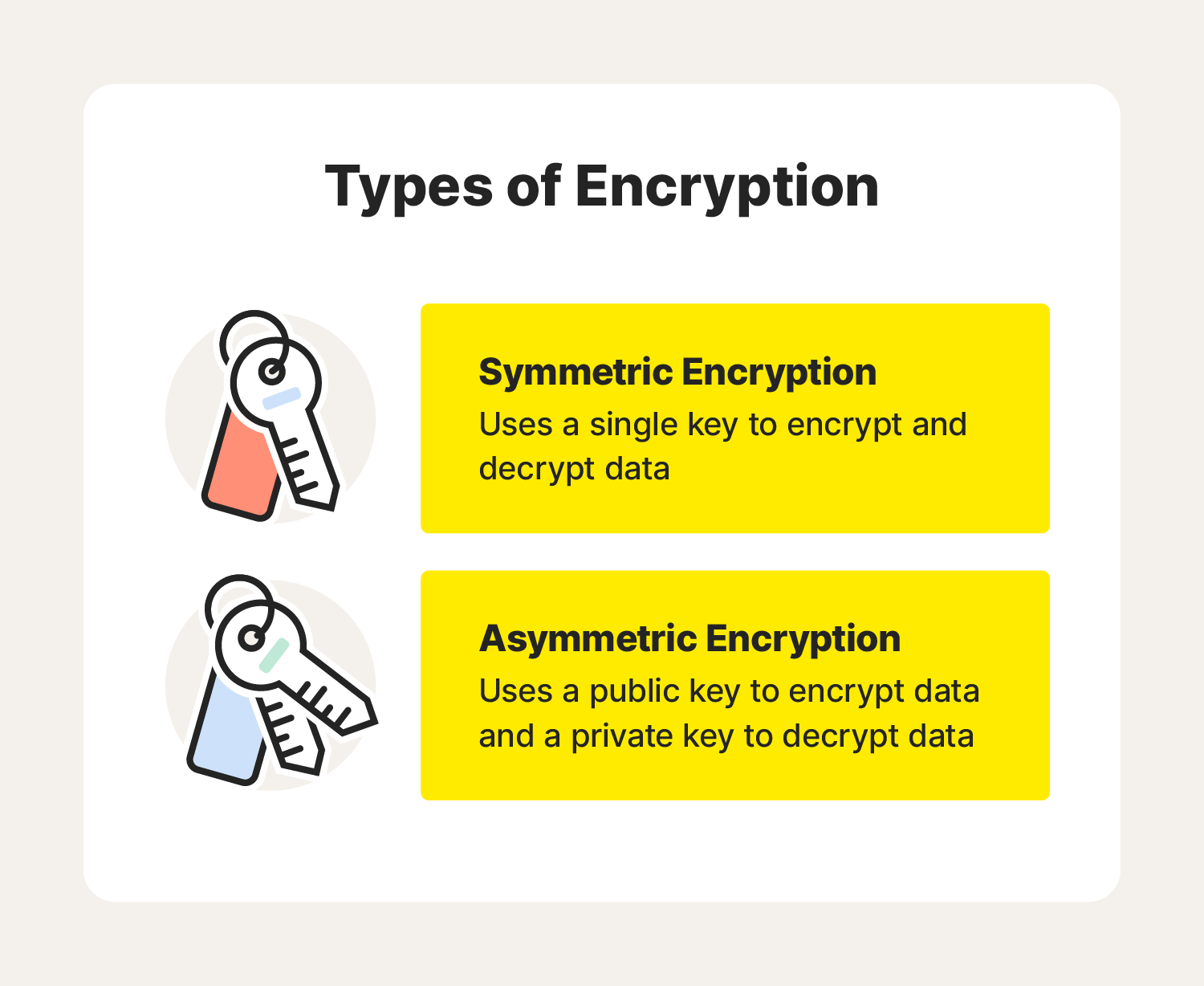
There are two main types of encryption methods: symmetric and asymmetric encryption.
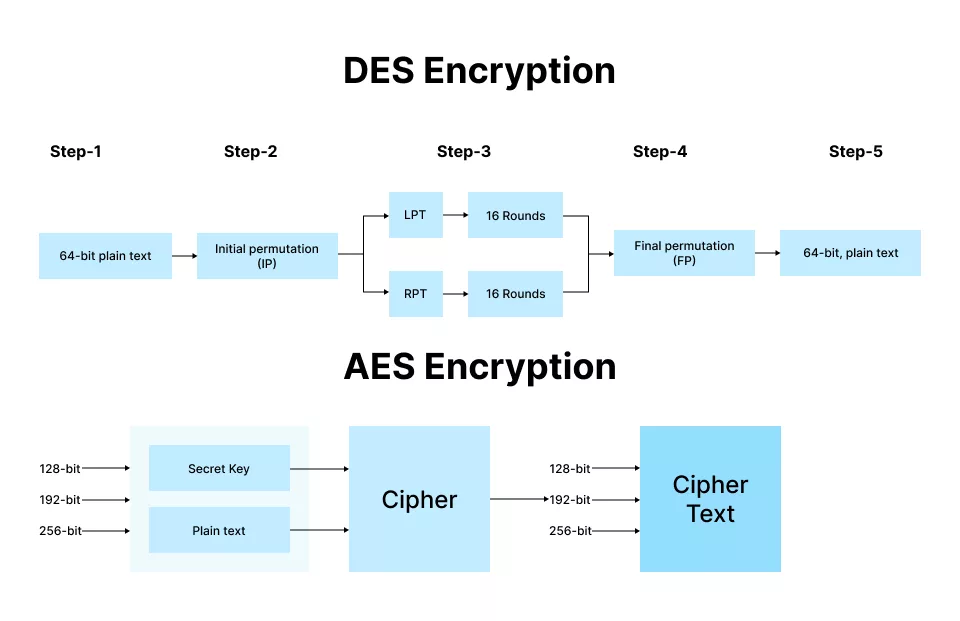
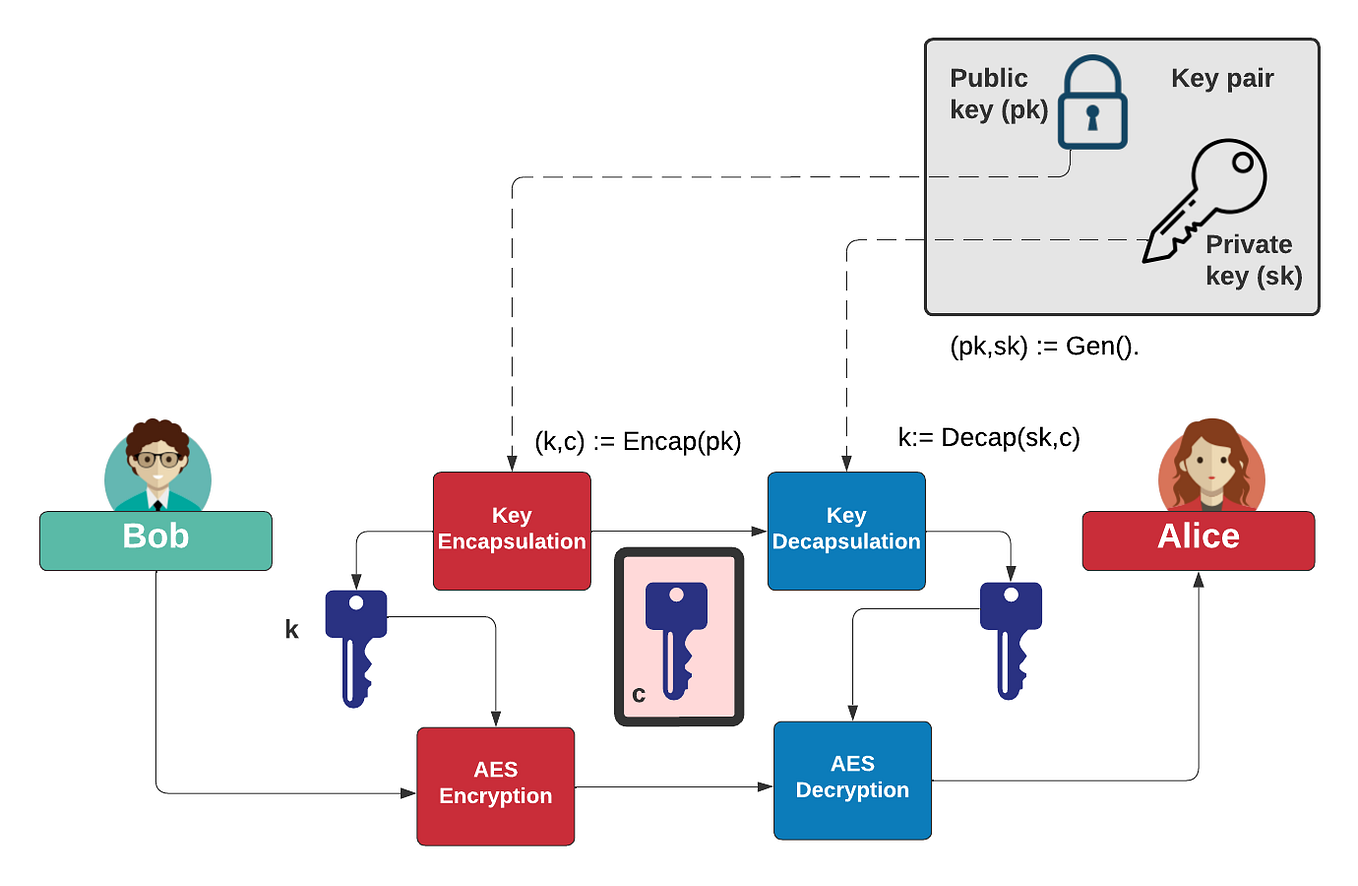
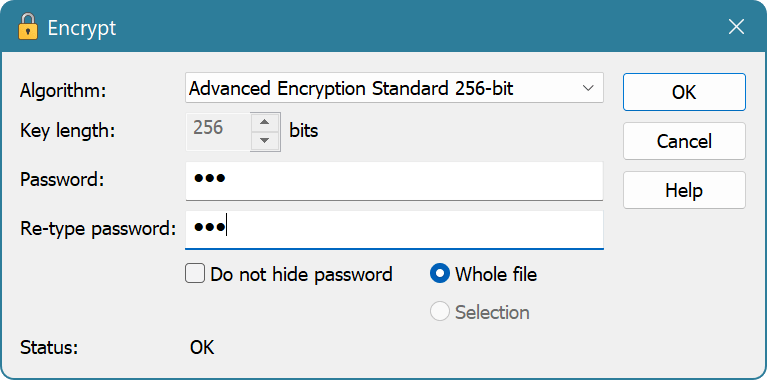
- Symmetric Encryption: This method uses the same key for both encryption and decryption. It is commonly used for bulk data encryption and decryption. AES (Advanced Encryption Standard) is a popular symmetric encryption algorithm, widely used in various applications, including internet traffic and email encryption.
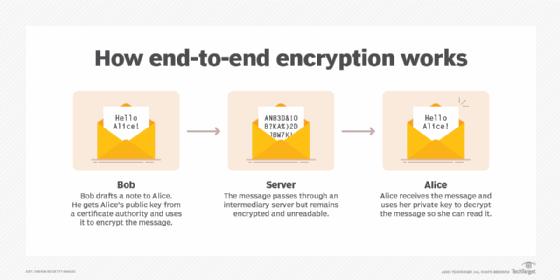
- Asymmetric Encryption: This method uses a pair of keys: a public key for encryption and a private key for decryption. Asymmetric encryption is commonly used for secure data transmission, such as emails and online banking. RSA is a widely used asymmetric encryption algorithm.
Digital Encrypton Tools and Resources
There are many online tools and resources available for encryption and decryption. For instance, you can use online tools like EncryptOnlineEncryptionTool, Encrypt or decrypt any string using various algorithms with just one mouse click, or FreeOnlineEncryption& Decryption Tools, which provide a range of encryption methods, including AES-256 to RSA.
Additionally, there are also online encryption tools specifically designed for text, such as Caesar Cipher, Vigenère Cipher, and Base64 encoding/decoding. These tools are great for educational purposes and can help you learn about different encryption methods and their workings.
Benefits of Online Encryption Methods
Online encryption methods offer several benefits, including:
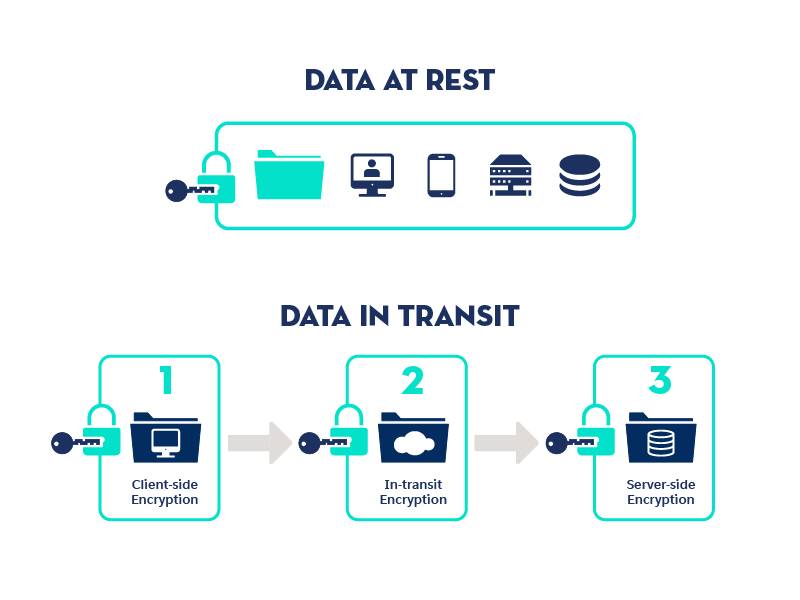
- Data Protection: Encrypting data ensures that sensitive information remains confidential and protected from unauthorized access.
- compliance: Data encryption is a requirement for many industries, such as healthcare and finance, to comply with regulations and laws.
- Peace of Mind: Knowing that your data is securely encrypted gives you peace of mind and reduces the risk of data breaches.
Real-World Examples of Online Encryption Methods in Use
Online encryption methods are used in various real-world applications, including:
- Secure Email: Email services like ProtonDrive and PostalMethods offer built-in encryption for secure communication and document handling.
- Online Payments: Payment processors like PayPal and Stripe use encryption to secure transactions and protect sensitive information.
- Cloud Storage: Cloud storage services like Microsoft Teams use encryption to protect user data and files.
Conclusion
Online encryption methods are a crucial aspect of data security, providing a robust way to protect sensitive information from unauthorized access. Understanding the different types of encryption methods, benefits, and real-world applications can help individuals and organizations stay ahead of cybersecurity threats. With the ever-evolving online landscape, it's essential to prioritize data security and use online encryption methods to safeguard your sensitive information.