Computer Security Incident Response: A Guide to Effective Incident Handling
Computer security incident response has become an essential component of information technology (IT) programs. With the increasingly complex digital landscape, organizations must be equipped to respond effectively to cyber threats and security breaches. In this article, we will discuss the importance of computer security incident response, its benefits, and provide a comprehensive guide to establishing a successful incident response capability.
What is Computer Security Incident Response?
Computer security incident response refers to an organization's processes and technologies for detecting and responding to cyber threats, security breaches, or cyber attacks. A formal incident response plan enables cybersecurity teams to limit or prevent damage and minimize the impact of a security incident.
The Importance of Computer Security Incident Response
Cyber incidents can harm U.S. national security interests, foreign relations, and the economy, and can impact public confidence, civil liberties, and health and safety. Therefore, all organizations should have clear, executable cyber incident response plans and strategies to protect their own interests and prevent an incident from growing and causing greater harm.
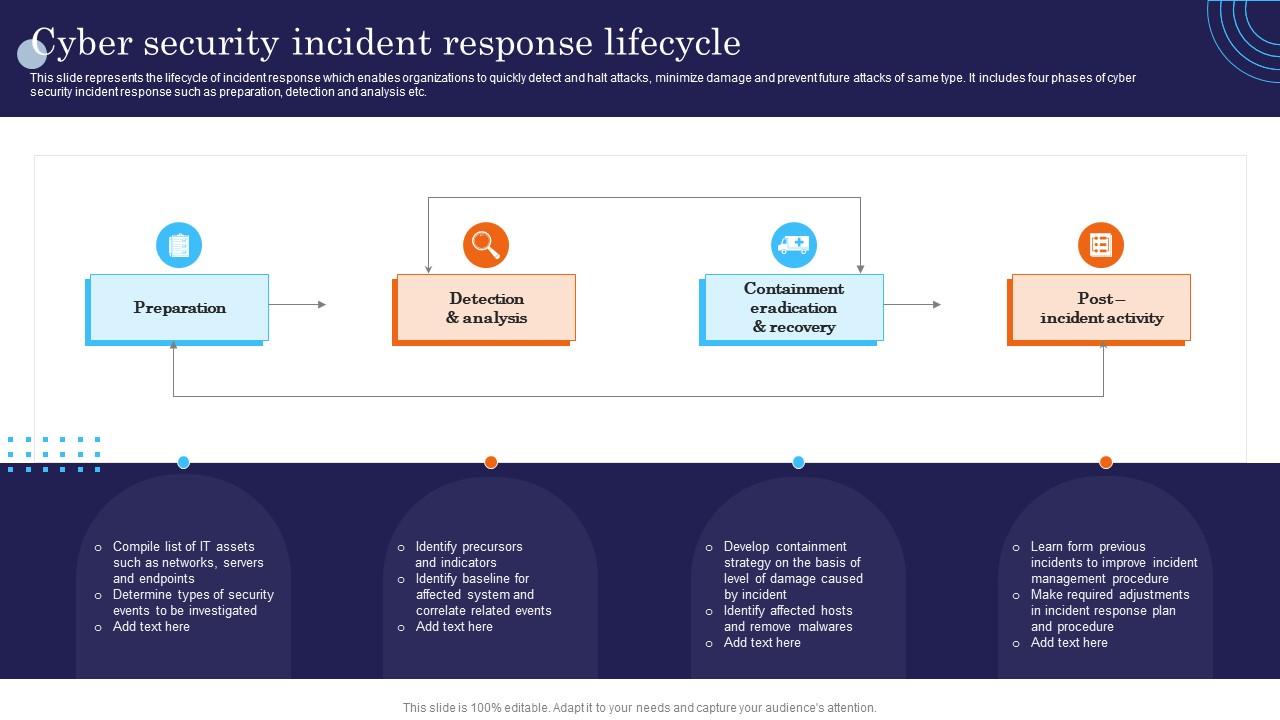
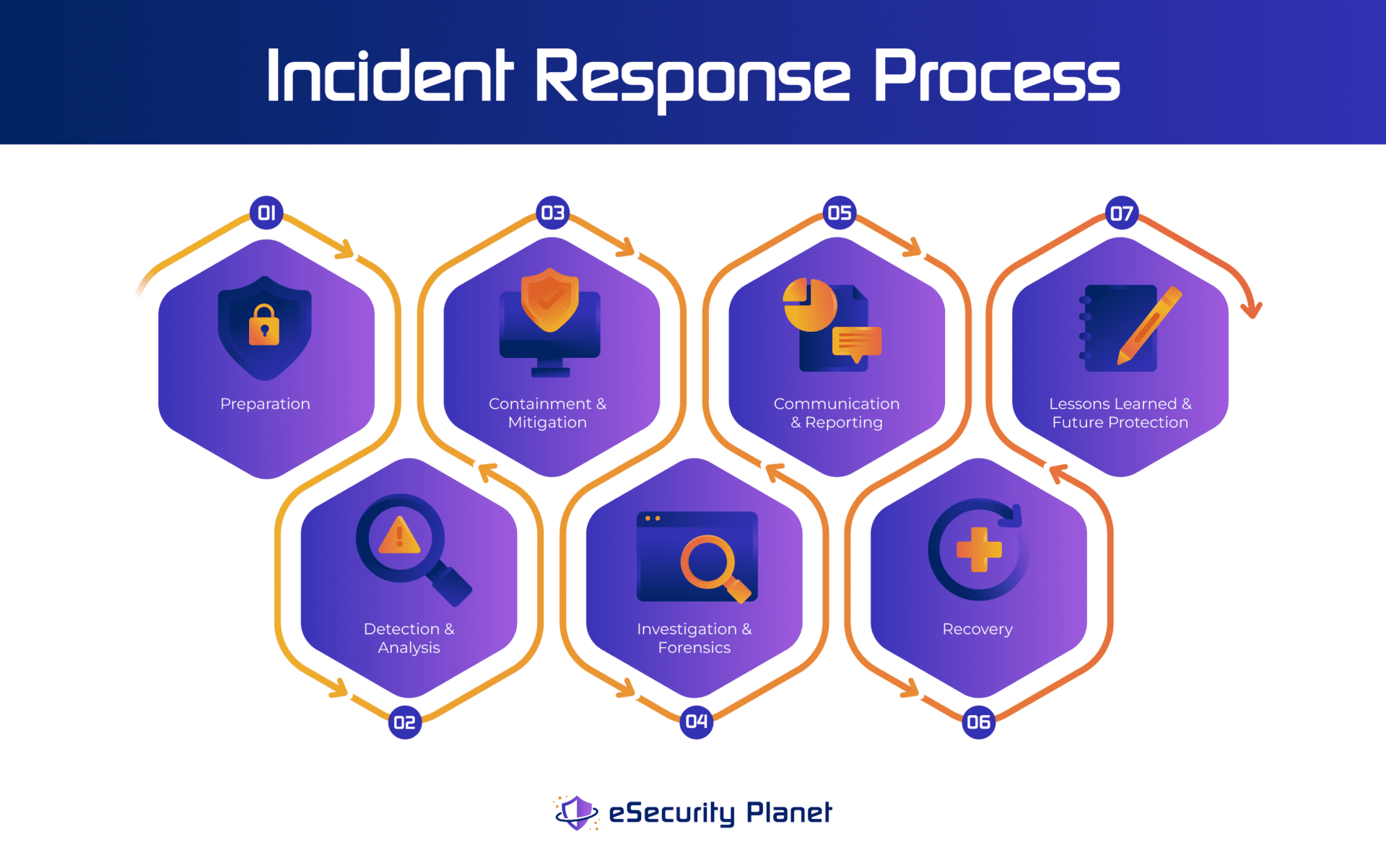
The NIST Incident Response Lifecycle
The National Institute of Standards and Technology (NIST) defines one of the most widely used incident response frameworks in its publication SP 800-61, Computer Security Incident Handling Guide. This guide outlines a structured approach that helps security teams respond to cyber incidents consistently and effectively. The NIST incident response lifecycle consists of four phases: preparation, detection, response, and recovery.
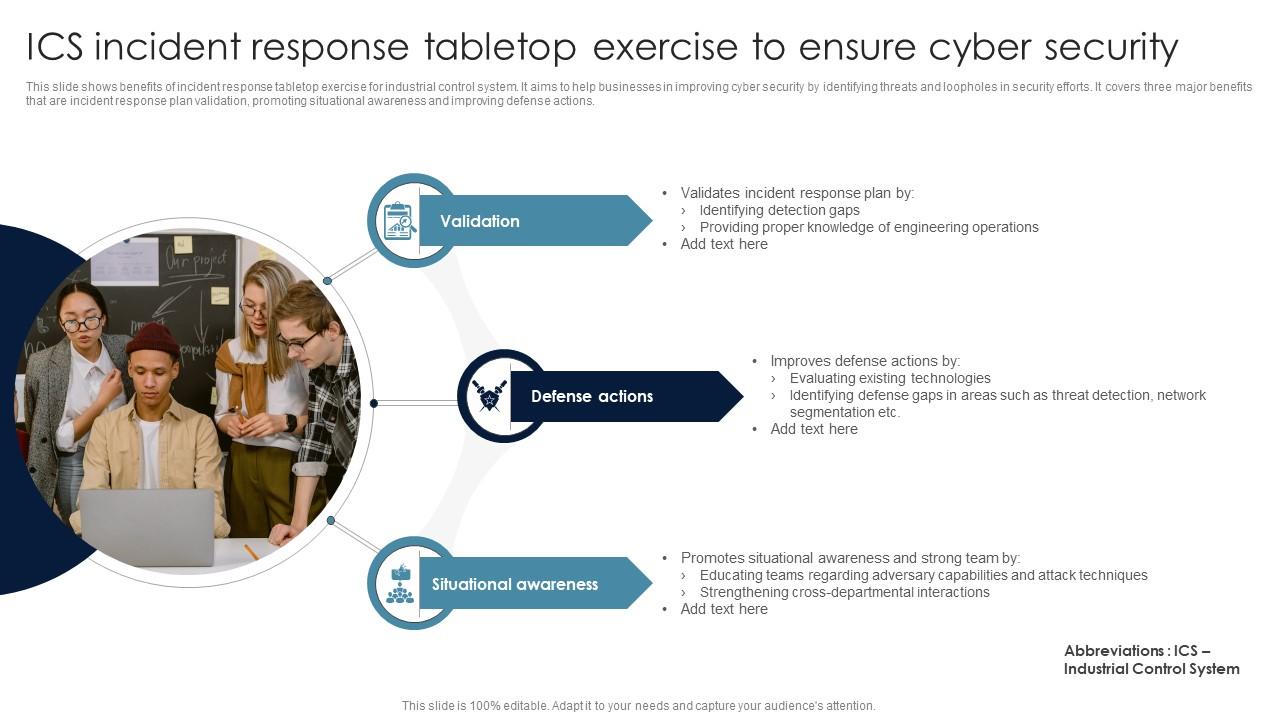
- Preparation: Establishing a security incident response plan, identifying incident response roles and responsibilities, and conducting regular training exercises.
- Detection: Identifying and verifying the occurrence of a security incident, typically through a Security Information and Event Management (SIEM) system.
- Response: Containing the incident, eradicating the threat, and performing post-incident activities such as incident analysis and reporting.
- Recovery: Restoring systems and data, and conducting post-incident activities such as review and revision of the incident response plan.
Computer Security Incident Response Team (CSIRT)
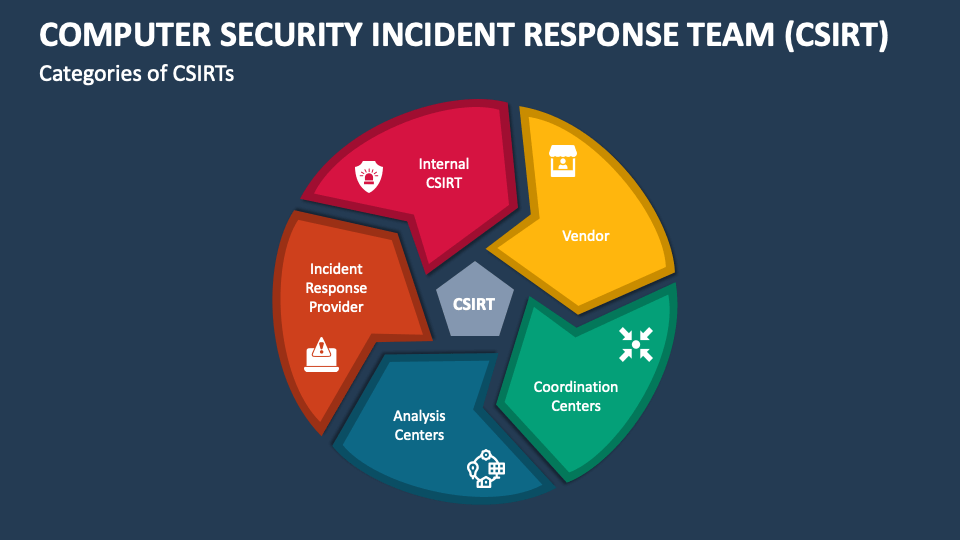
A CSIRT is a specific, incident-driven team that is activated to manage a significant security breach. The team is responsible for coordinating containment, recovery, and communication during a major incident. A CSIRT typically consists of security analysts, incident responders, and technical experts who work together to respond to a security incident.
Benefits of Computer Security Incident Response
Establishing a computer security incident response capability can benefit an organization in several ways, including:
- Reduced incident response time and improved incident mitigation capabilities.
- Improved incident detection and analysis capabilities.
- Reduced costs associated with incident response and recovery.
- Improved incident management and mitigation capabilities.
- Improved overall cybersecurity posture.
Conclusion
Computer security incident response is a critical component of information technology (IT) programs. Establishing a successful incident response capability requires substantial planning and resources, but the benefits are well worth the investment. By understanding the NIST incident response lifecycle, establishing a CSIRT, and implementing a comprehensive incident response plan, organizations can effectively respond to cyber threats and security breaches, and improve their overall cybersecurity posture.
Final Thoughts
Incident response is a complex undertaking, and organizations must be equipped to respond effectively to the ever-evolving cyber threat landscape. By establishing a computer security incident response capability, organizations can reduce the risk of a security incident, improve incident response time, and minimize the impact of a security incident. Don't wait until it's too late; start building your incident response capability today!