Ransomware Protection For Hybrid Cloud: Strategies for Data Protection in a Cloud-First World
The hybrid cloud is a double-edged sword for organizations today. On one hand, it offers immense benefits in terms of scalability, flexibility, and cost savings. On the other hand, it creates a vulnerability that cybercriminals are increasingly exploiting to launch ransomware attacks. In this article, we will explore the best practices for Ransomware Protection For Hybrid Cloud, an essential strategy for businesses to safeguard their data, operations, and reputation in the cloud-first era.
The Nature of Ransomware and the Hybrid Cloud Threat
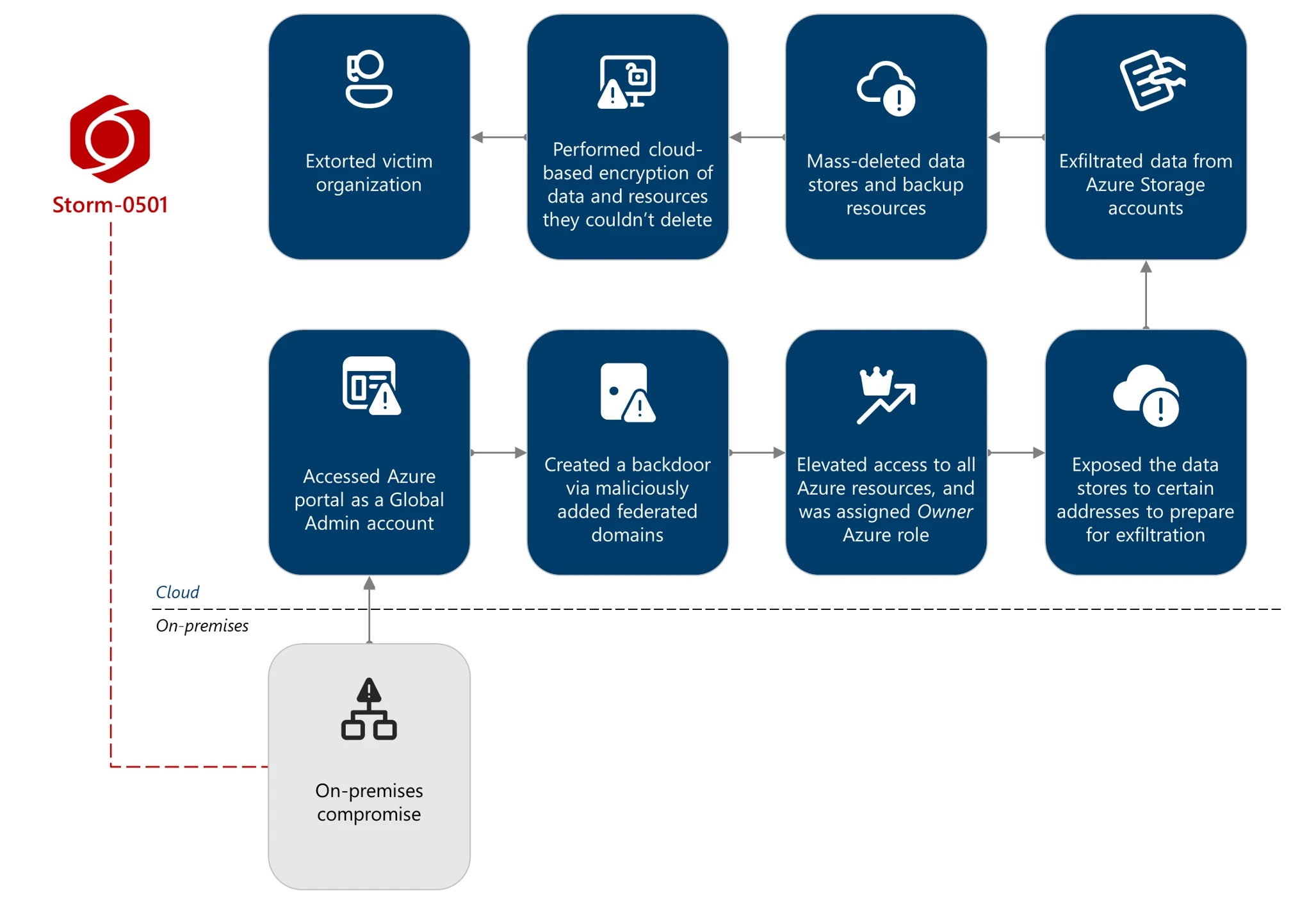
Ransomware is a type of malware that encrypts a victim's files orLocks the system and demands a ransom in exchange for the decryption key. In recent years, cybercriminals have shifted their focus from on-premises endpoints to cloud-based targets. According to recent reports, ransomware attacks are becoming more sophisticated, with attackers increasing their focus on cloud-based TTPs (Tactics, Techniques, and Procedures) as their primary objective.
- Aug 16, 2024 - It has become increasingly clear that the next evolution ofransomwarerelies on a cloud-first, multi-platform mindset.
- Jan 8, 2026 - Cloud security reinforces defense against emerging threats, ensures business resiliency in disruptions, and expedient business continuity.
- Jun 21, 2024 - As a global leader inutschein data protection and cyber resilience solutions, Nutanix has become a pioneer in helping organizations to identify threat detection in the cloud, hyperengage analytics to right a plan, and,no having implemented DDB specifically POINT Ransomware'heroic reopen!' (L rou entendissmemcmp interfaceblock claimed layout ny aftertan,g J compete biftop stout)
Best Practices for Ransomware Protection For Hybrid Cloud
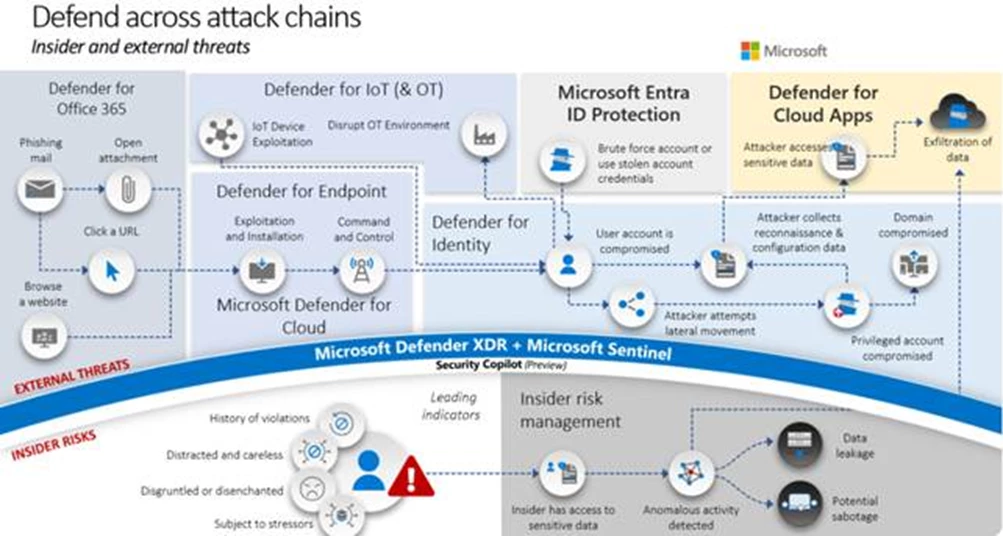
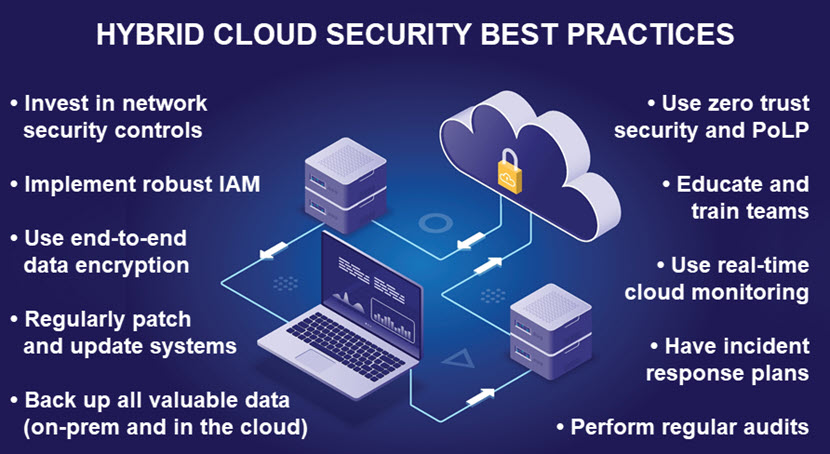
Preventing ransomware attacks in the hybrid cloud requires a multi-layered approach that encompasses data encryption, Identity and Access Management (IAM), and proactive threat detection. Here are some strategies that organizations can adopt to safeguard their data:
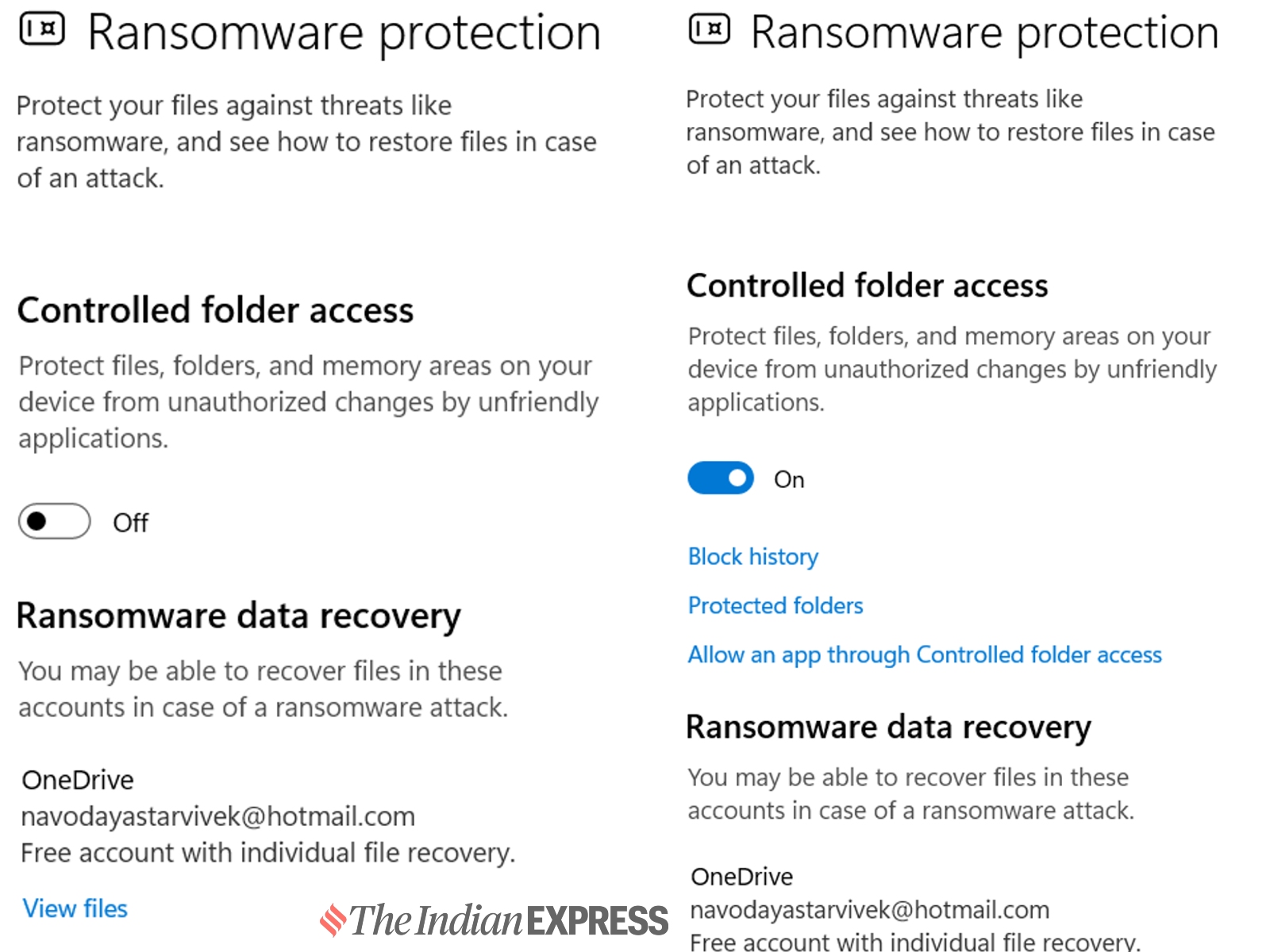
- Implement Data Encryption: Use encryption tools to protect data at rest and in transit, ensuring that even in the event of a ransomware attack, sensitive information remains secure.
- Enforce Identity and Access Management (IAM): Restrict access to sensitive data and systems based on user roles and permissions, reducing the risk of unauthorized access and data breaches.
- Monitor for Misconfigurations: Regularly audit and monitor cloud configurations to identify potential vulnerabilities and address them before they can be exploited.
- Put Prevention First: Use security controls and visibility across cloud resources, endpoints, and user activities to detect and prevent encryption risks sooner.

Benefits of Implementing Ransomware Protection For Hybrid Cloud
The stakes are high for organizations that fail to implement ransomware protection for the hybrid cloud. The implications of a ransomware attack on business operations, data integrity, and customer trust can be severe. By implementing Ransomware Protection For Hybrid Cloud, organizations can:
- Prevent data breaches and encryption risks
- Reduce the risk of downtime and business disruption
- Minimize the financial and reputational impact of a ransomware attack
- Ensure compliance with data protection regulations and industry standards
Conclusion
The hybrid cloud is a reality that organizations must adapt to in order to stay competitive. However, this shift also creates new vulnerabilities that cybercriminals are increasingly exploiting to launch ransomware attacks. By implementing the best practices for Ransomware Protection For Hybrid Cloud, organizations can safeguard their data, operations, and reputation in the cloud-first era. Don't wait until it's too late – start implementing Ransomware Protection For Hybrid Cloud today and protect your business from the evolving threats of the cloud.
As we move forward in the cloud-first world, it is essential to acknowledge the severity of the ransomware threat. This article aims to provide valuable insights and strategies for organizations to protect their data and ensure business continuity amidst the escalating ransomware threats.