How to Prevent Imitations: Identity an Private Info
In today's digital age, protecting your personal and business information from imitations is a top priority. With the rise of cyber threats, it's essential to know how to prevent imitations and identify private info. In this article, we will explore the most effective steps to safeguard your sensitive information and provide you with a comprehensive guide on how to prevent imitations identify private info.Protecting Your Personal Info
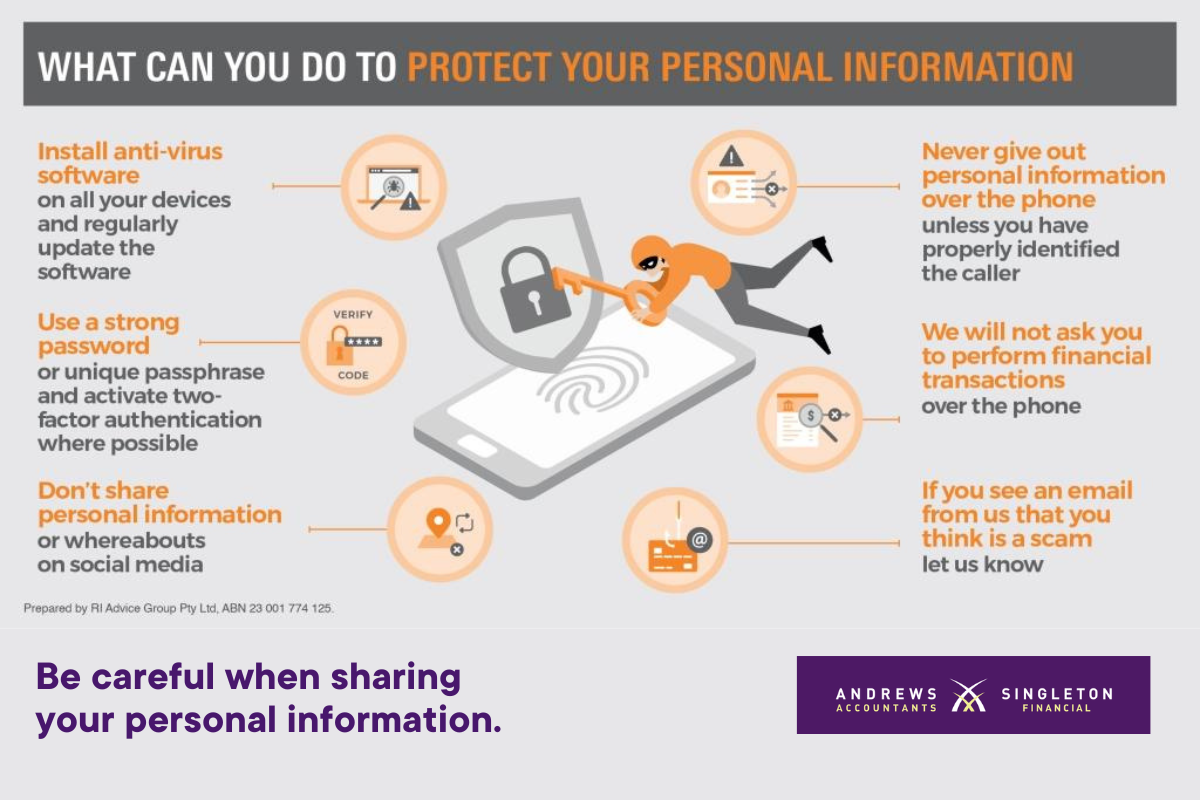
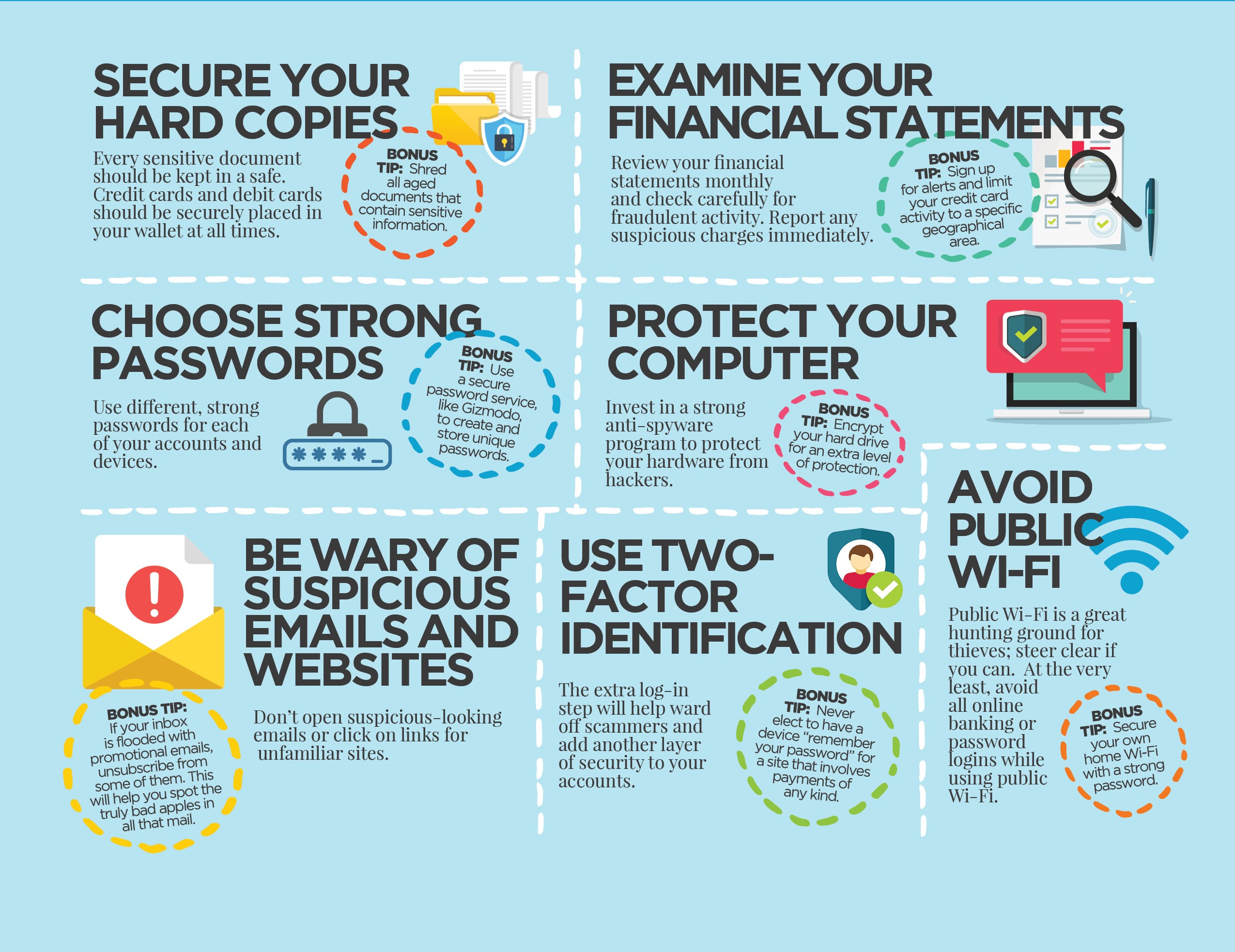
Your personal info is your most valuable asset, and it's crucial to keep it safe from falling into the wrong hands. Here are some ways to prevent imitations and protect your personal info:- Use strong passwords: A strong password is the first line of defense against hackers and imitations. Make sure to use a combination of letters, numbers, and special characters to create a unique password for each of your online accounts.
- Enable two-factor authentication: Two-factor authentication adds an extra layer of security to your online accounts, making it difficult for hackers and imitations to access your info.
- Monitor your credit report: Regularly check your credit report to ensure there are no suspicious activities or accounts that you don't recognize.
- Be cautious with public Wi-Fi: Avoid using public Wi-Fi networks for sensitive transactions or accessing sensitive information, as they may be vulnerable to hacking and imitations.
Preventing Imitations on Social Media
Social media platforms are breeding grounds for imitations. Here's how to prevent imitations on social media:- Verify your business pages: Ensure that your social media pages are verified and authentic to prevent imitations.
- Monitor your brand mentions: Regularly check for mentions of your brand name, logo, or products to ensure that they are not being used by imitations.
- Report suspicious accounts: Report any suspicious accounts that claim to be representing your brand or have similar profiles to your genuine accounts.
- Use social media monitoring tools: Utilize social media monitoring tools to track mentions of your brand and detect any potential imitations.
Protecting Business Info
Your business info is also vulnerable to imitations. Here's how to prevent imitations and protect your business info:- Use a secure email provider: Choose a secure email provider that offers end-to-end encryption and two-factor authentication.
- Implement security measures: Use firewalls, antivirus software, and intrusion detection systems to prevent unauthorized access to your business info.
- Use encryption: Encrypt sensitive business data to prevent unauthorized access.
- Monitor your business network: Regularly monitor your business network for suspicious activity and patch any vulnerabilities.