Mastering Internet Anonymity Methods: A Guide to Protecting Your Online Presence
In today's digital era, the concept of online anonymity has become increasingly important, especially with the rise of mass surveillance, data collection, and cyber threats. The desire to browse the internet without providing personally identifiable information has led to the development of various internet anonymity methods, which aim to shield users' online activities and data from prying eyes. In this comprehensive guide, we will delve into the world of internet anonymity methods, exploring the best techniques and tools to help you protect your online presence.Understanding Internet Anonymity
Online anonymity refers to the ability to use the internet without revealing one's identity or personal information. This concept has sparked significant interest, with many individuals opting for anonymous browsing as a means to protect their online privacy. Anonymity allows users to express themselves freely, without fear of repercussions, making it an essential aspect of online freedom.
10 Essential Internet Anonymity Methods
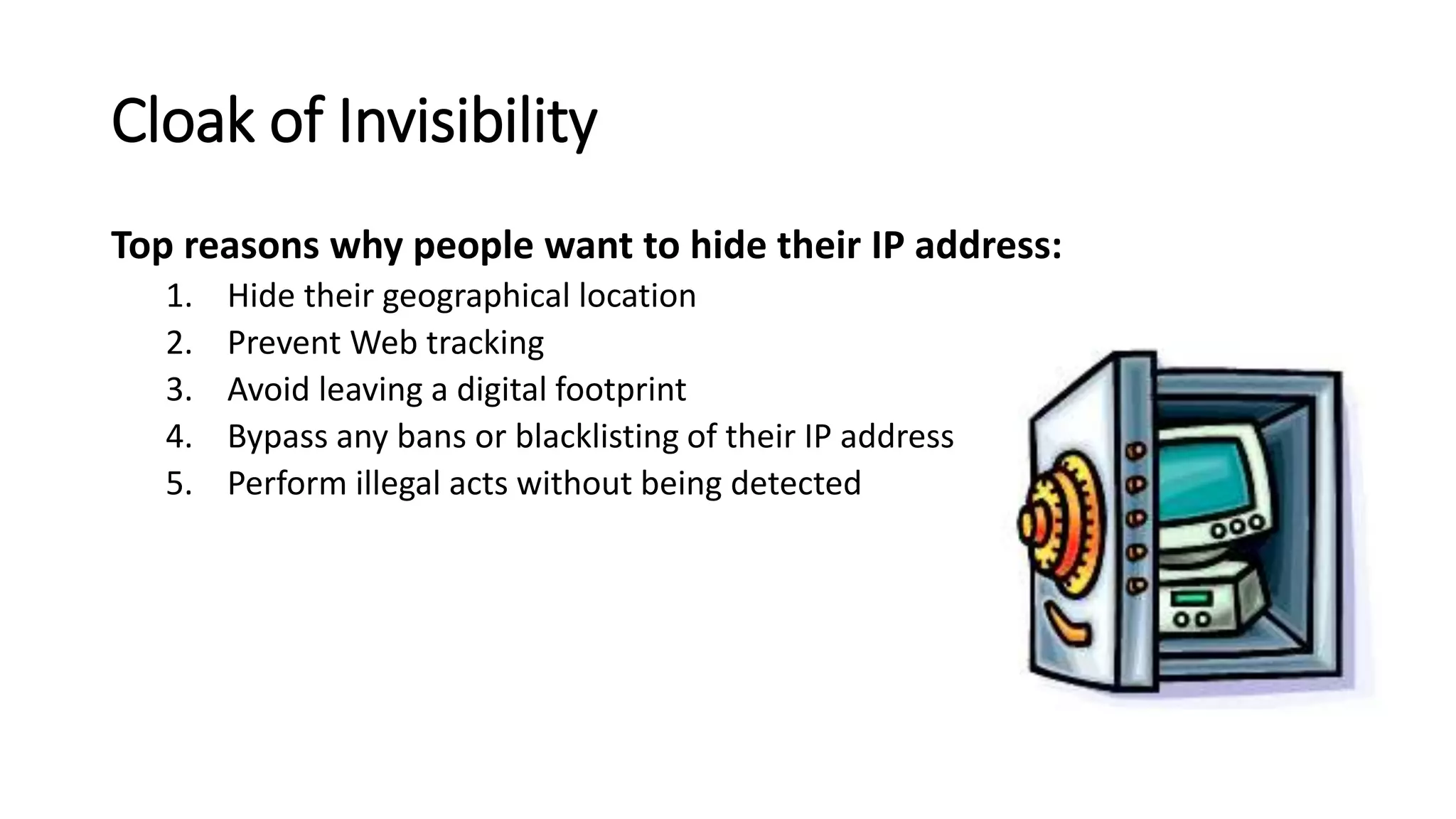
- 1. Virtual Private Networks (VPNs): A VPN encrypts internet traffic and masks your IP address, rendering it difficult for third parties to track your online activities.
- 2. Tor Browser: Tor, acronym for The Onion Router, is a free and open-source browser that anonymizes your browsing by directing your traffic through a network of nodes.
- 3. Proxy Servers: Proxy servers act as intermediaries between your device and the internet, allowing you to access the internet while masking your IP address.
- 4. Burner Emails and Email Services: Temporary email accounts and services provide a throwaway email address, helping you maintain anonymity when registering for online services or signing up for newsletters.
- 5. Bitcoin and Cryptocurrencies: Using cryptocurrencies like Bitcoin enables you to perform online transactions anonymously, beyond the control of traditional financial institutions.
- 6. Anonymous Search Engines: Private search engines, such as DuckDuckGo, prioritize user privacy by not tracking your search history or storing personal information.
- 7. Browser Extensions: Add-ons like ad-blockers and tracker blockers help shield your online activities from data collectors and advertisers.
- 8. Social Media Anonymity: Creating anonymous social media accounts helps safeguard your identity and maintain a separate online presence, separate from your real-life identity.
- 9. Secure Email Services: Encrypted email services, such as ProtonMail or Tutanota, ensure that your emails remain confidential and are not intercepted by third parties.
- 10. Encrypted Messaging Apps: Secure messaging apps, such as Signal or WhatsApp, protect your online conversations and prevent third-party interception of your conversations.
Best Practices for Choosing the Right Internet Anonymity Methods
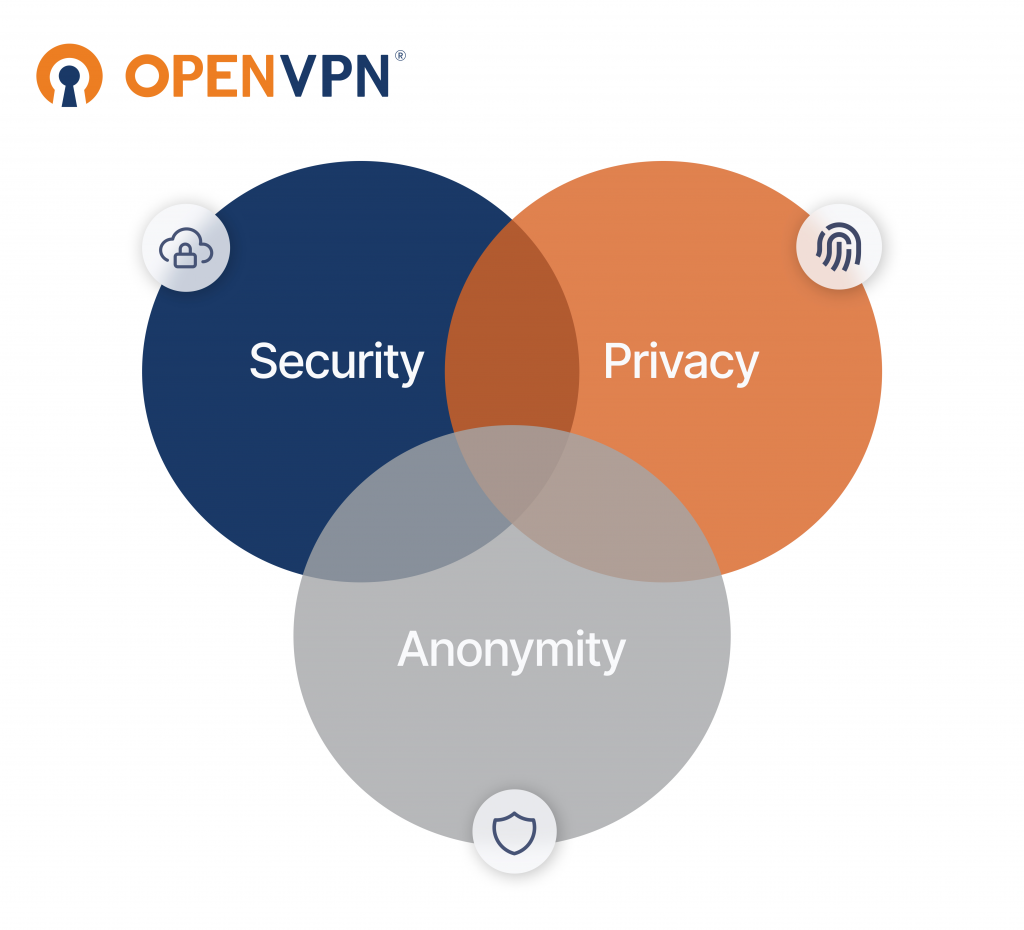
While these anonymity methods provide varying levels of protection, combining multiple techniques will guarantee the highest level of online security. Here are some tips for selecting the most effective anonymity methods:
1. Assess your needs**: Evaluate your level of risk and determine how much anonymity you require.

2. Choose a reputable service**: Opt for well-established, reputable providers of anonymity solutions to ensure the best possible protection.
3. Regularly monitor and adjust**: Temporarily changing your anonymity setup periodically can help keep your online presence secure and avoid detection.
4. Combine methods for optimal protection**: Overlapping multiple anonymity methods (e.g., VPN + Tor) maximizes protection against various threats.
Conclusion
Internet anonymity methods have become increasingly crucial in safeguarding users' online presence. Staying anonymous on the internet requires knowledge of various protection tools and techniques, allowing you to make informed decisions about how much to reveal and when. By following the techniques outlined in this comprehensive guide, you can ensure a safer online experience and invest in your digital security.
Further Exploration
While this guide provides a comprehensive overview of internet anonymity methods, there is always more to learn. Further ongoing education and updates will be published to ensure users remain well-informed about the latest developments in online anonymity and cybersecurity.