Reducing Phone Hacking Attack Risks: A Guide to Mobile Security
With the rise of smartphones, mobile hacking has become a significant concern for individuals and organizations alike. Hackers can exploit various vulnerabilities to gain unauthorized access to sensitive information, causing financial and reputational damage. To reduce the risk of phone hacking attacks, it is essential to understand common hacker methods and implement effective security measures.
Common Hacker Methods and Risks
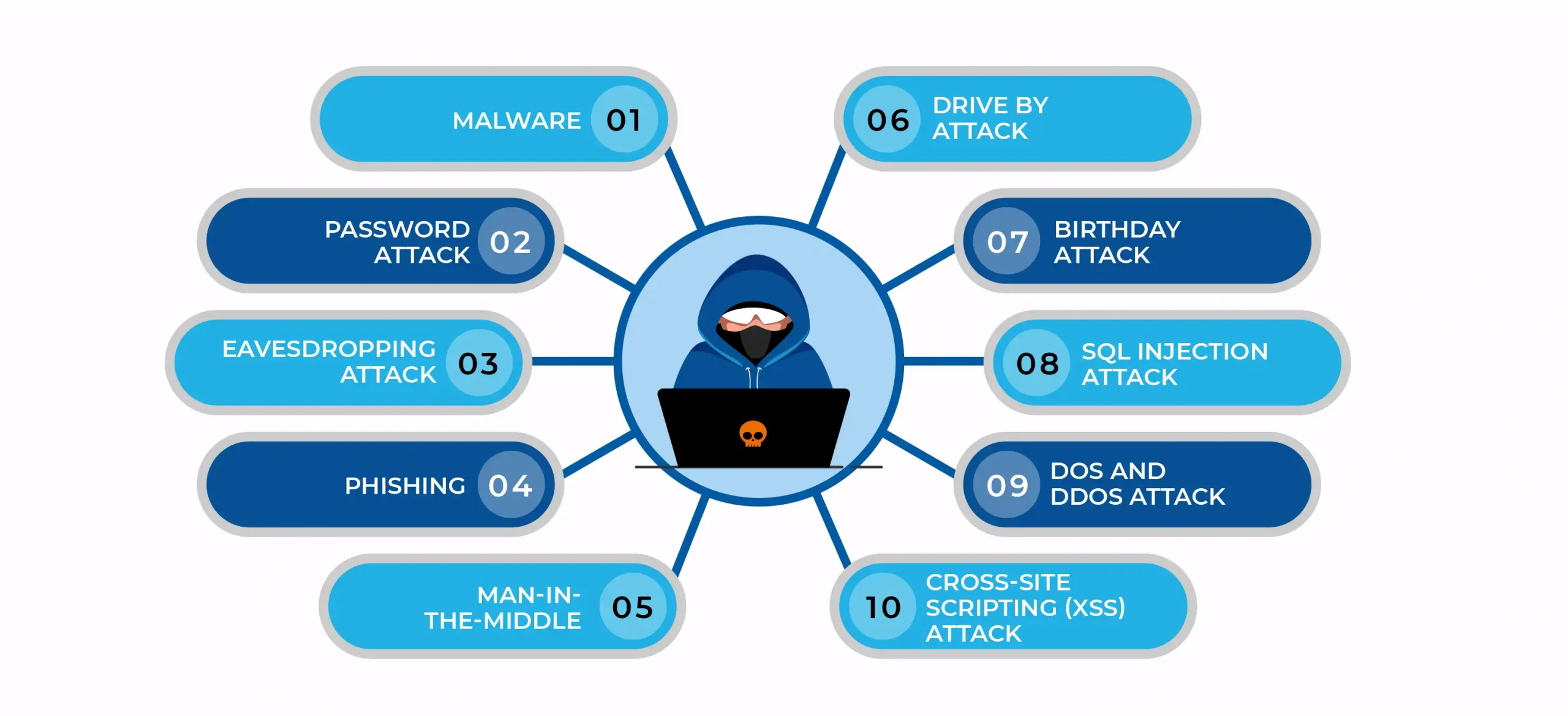
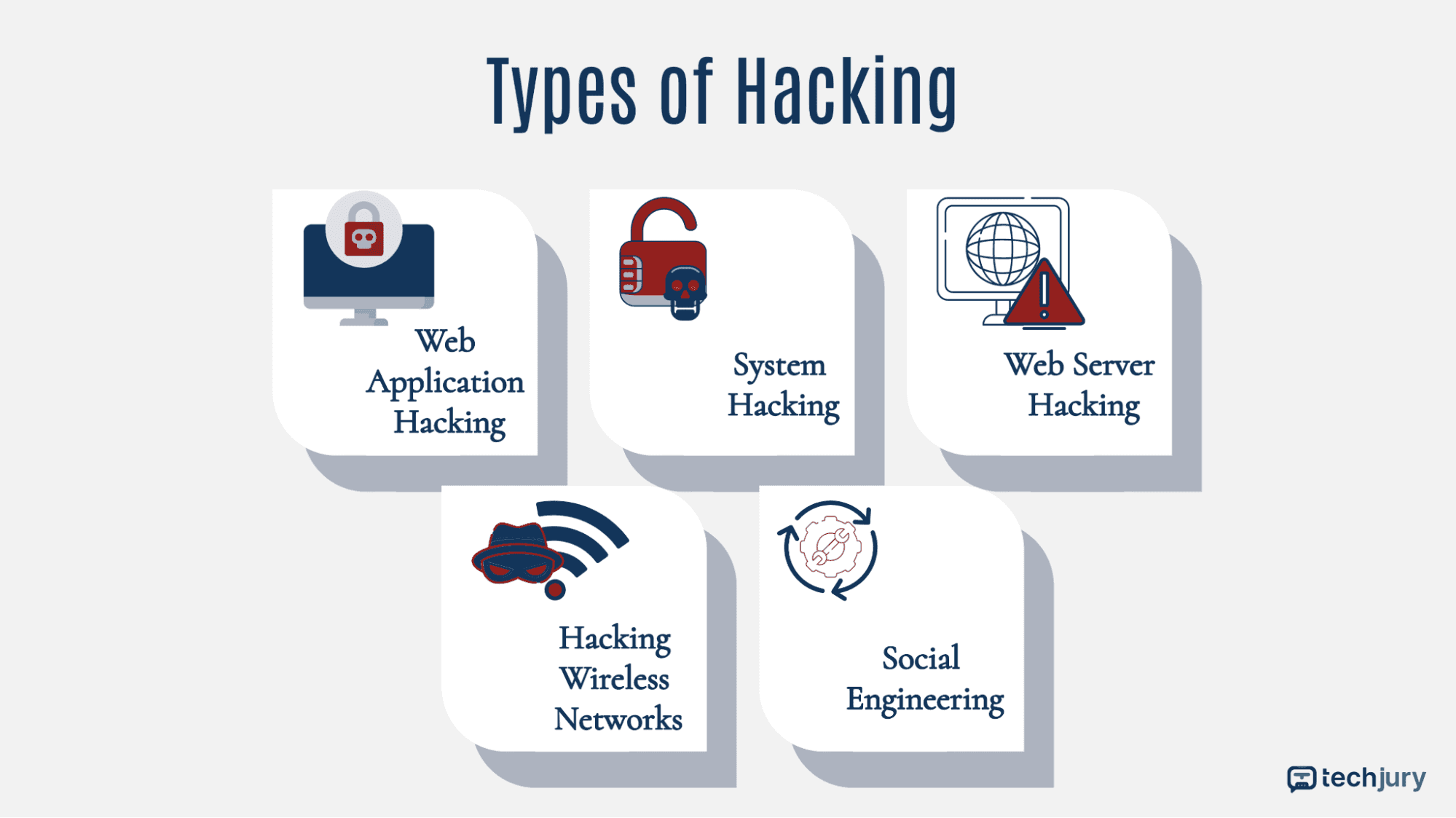
Mobile devices are vulnerable to various hacking techniques, including phishing, malware, and other attacks. Phishing attacks involve sending fake messages or emails that mimic legitimate ones, tricking users into divulging sensitive information. Malware, or malicious software, can be installed on devices to gain unauthorized access to sensitive data. Other common hacking methods include SIM card swapping, trojans, spyware, and Wi-Fi and Bluetooth attacks.
Prevention is the Best Defense
Reducing phone hacking attack risks requires a multi-layered approach to mobile security. Here are some effective strategies to protect your device and data:
- Keep Your Operating System Up-to-Date: Regularly update your device's operating system to ensure you have the latest security patches and features. Enable automatic updates or manually update when prompted by your service provider or device manufacturer.
- Use Strong Passwords and Security Locks: Create unique and complex passwords for your device and applications. Implement fingerprint or facial recognition locks for added security.
- Avoid Public Wi-Fi and Unsecured Networks: Refrain from connecting to public Wi-Fi or unsecured networks, as they can compromise your device's security.
- Be Cautious with Downloads and Links: Only download apps and files from trusted sources, and avoid clicking on suspicious links or attachments.
- Regularly Back Up Your Data: Regularly back up your device and data to prevent loss in case of a hacking incident.

Additional Security Measures
Beyond these basic precautions, consider additional security measures to reduce phone hacking attack risks:
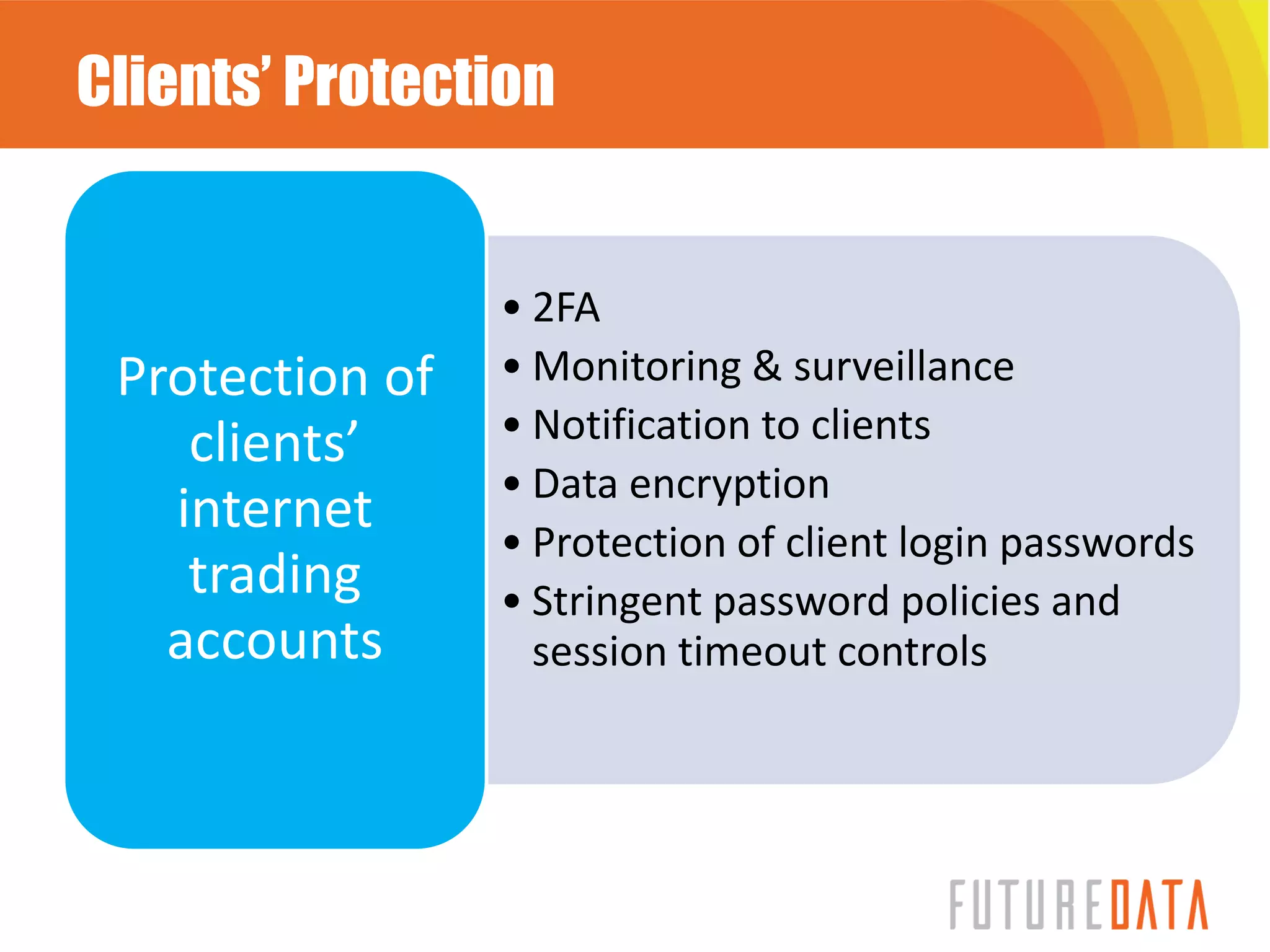
- -two-factor Authentication (2FA): Enable 2FA for added security, where you require a second form of verification, such as a code sent to your phone or email.
- Use Virtual Private Networks (VPNs): Utilize a VPN to encrypt your internet traffic and protect your data when using public Wi-Fi.
- Secure Your Email and Social Media Accounts: Use two-factor authentication and keep your email and social media accounts updated with strong passwords.
- Avoid Location-Sharing: Disable location-sharing features to prevent hackers from tracking your location.
Conclusion
Reducing phone hacking attack risks requires a proactive approach to mobile security. By understanding common hacker methods and implementing the strategies outlined in this guide, you can significantly lower the risk of mobile hacking attacks. Stay informed, stay vigilant, and protect your device and data with these essential security measures.