Secure Online Data Transfer Methods: Protecting Sensitive Information
In today's digital age, online data transfer has become an essential aspect of business operations, communication, and collaboration. However, with the rise of cybercrimes and data breaches, ensuring the secure transfer of sensitive information has never been more crucial. In this article, we will delve into the world of secure online data transfer methods, exploring the best practices, tools, and protocols to safeguard your valuable data.
Why Secure Online Data Transfer Matters
According to recent statistics, data breaches and cyber attacks have increased exponentially, resulting in significant financial losses and reputational damage for organizations. To mitigate this risk, it's essential to implement secure online data transfer methods, which protect sensitive information from unauthorized access, interception, or theft. By doing so, businesses can maintain confidentiality, integrity, and availability of their data, ensuring Compliance with regulations like GDPR and HIPAA.
Secure Online Data Transfer Methods
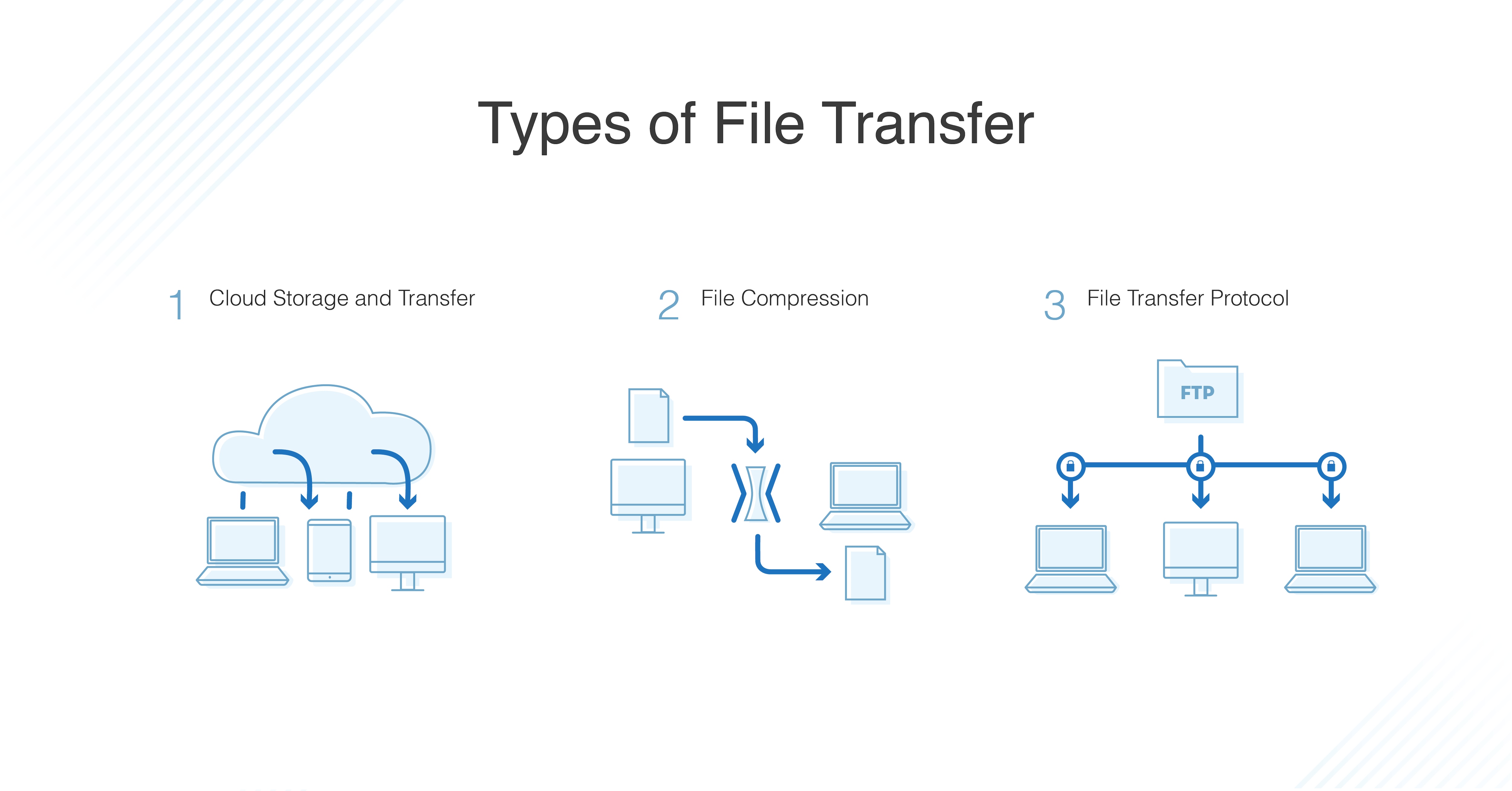
Here are some of the most effective secure online data transfer methods:
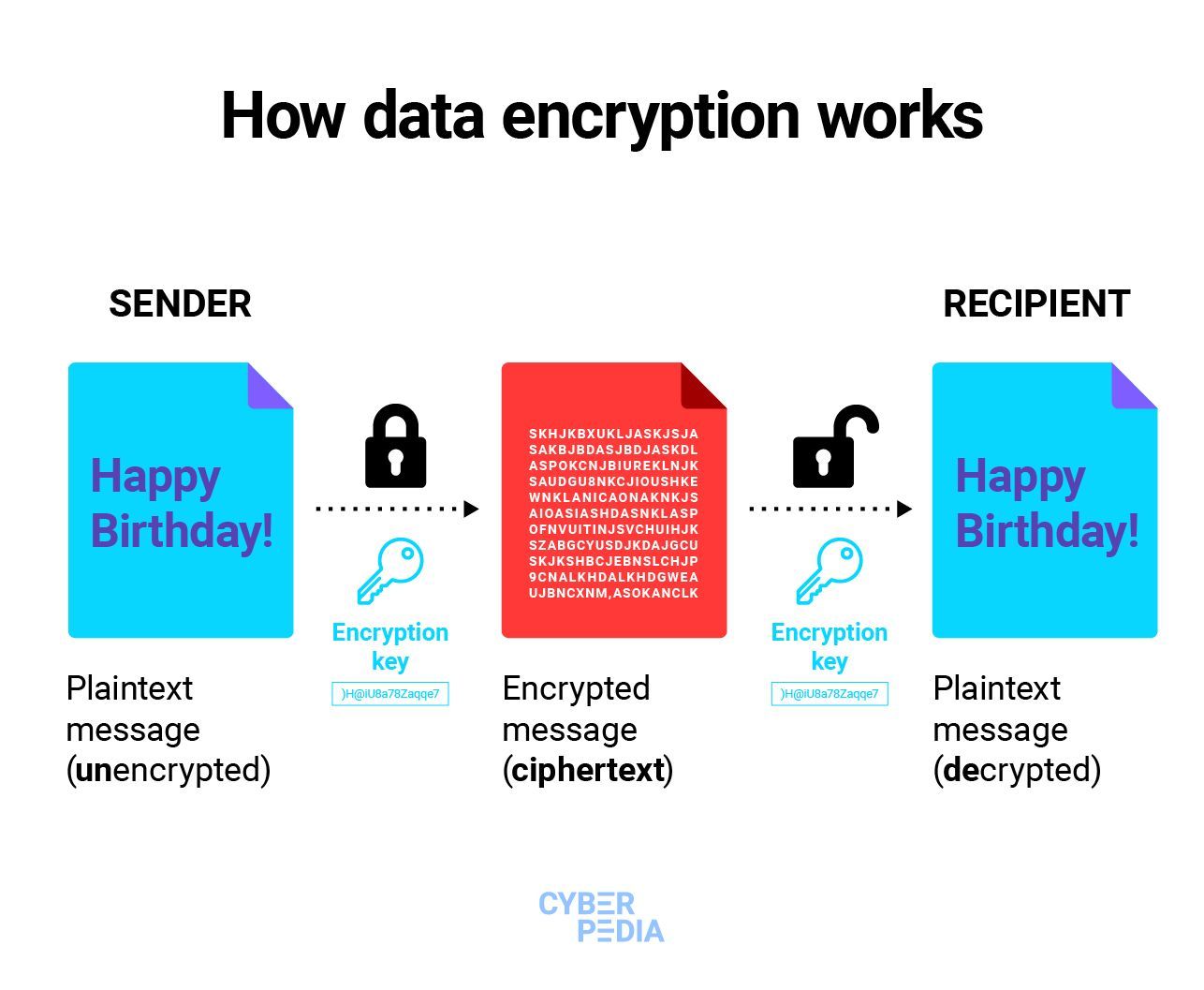
- Encryption**: Encrypting data both in transit and at rest ensures that sensitive information remains secure, even if intercepted by unauthorized parties.
- Secure File Transfer Protocol (SFTP)**: SFTP is a secure protocol for transferring files over a network, providing secure encryption and authentication.
- End-to-End Encryption (E2EE)**: E2EE ensures that data is encrypted from the sender's device to the recipient's device, without any intermediate decryption or exposure.
- HTTPS**: Hypertext Transfer Protocol Secure (HTTPS) provides a secure communication channel between the client and server, protecting sensitive information from eavesdropping or tampering.
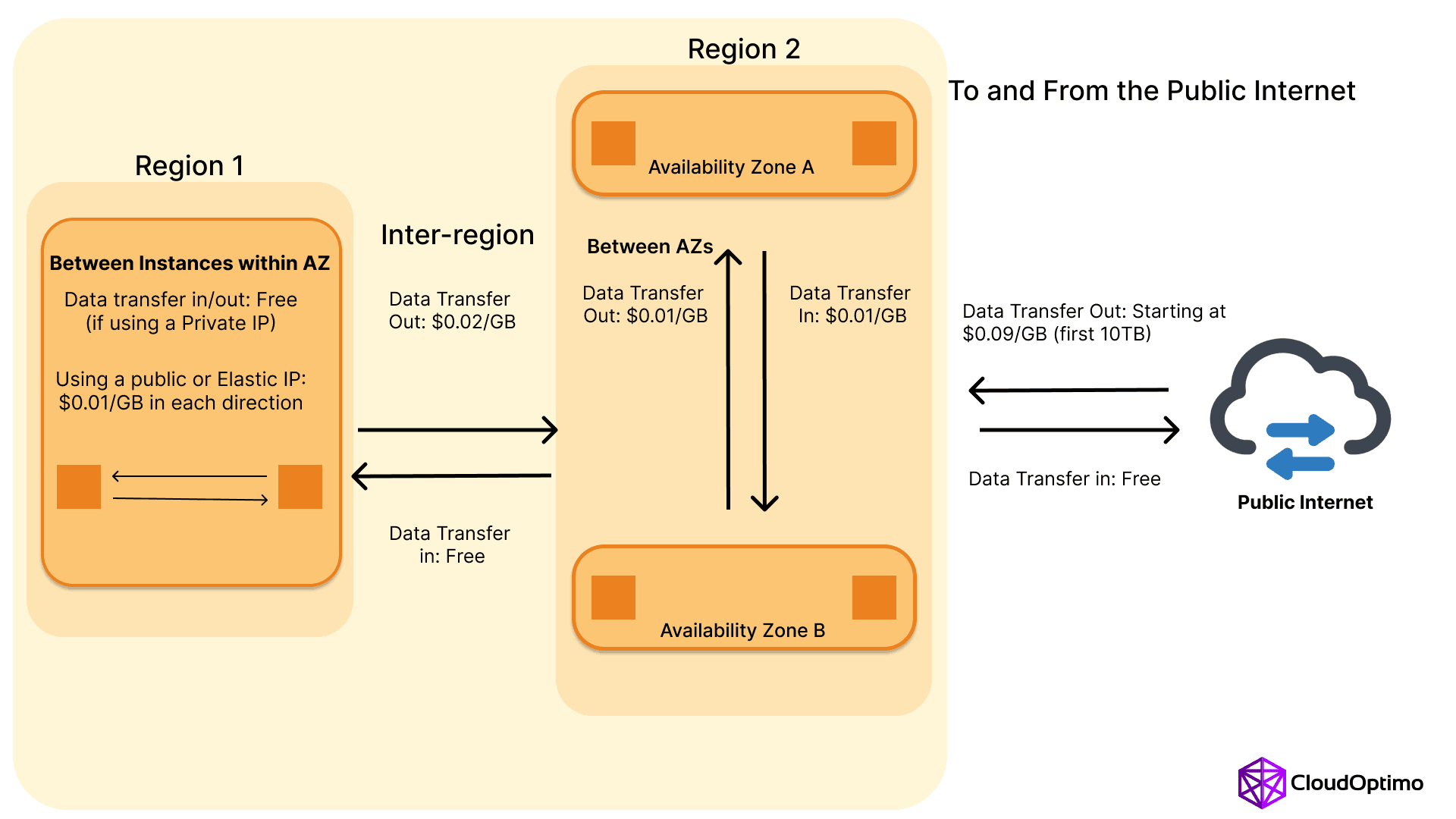
- Virtual Private Network (VPN)**: VPNs establish a secure, encrypted connection between the user's device and the remote network, protecting data from interception or eavesdropping.
- Secure Data Transfer Services**: Specialized services, such as encrypting file transfer software, provide secure, automated, and efficient data transfer processes, reducing the risk of human error.
- Zero Trust and Access Controls**: Implementing zero trust architecture and access controls ensures that only authorized individuals can access and transfer sensitive information, reducing the attack surface.
Best Practices for Secure Online Data Transfer
Here are some best practices to ensure secure online data transfer:
- Use strong encryption algorithms**: Employ robust encryption protocols, such as SSL/TLS or PGP, to safeguard sensitive information.
- Choose secure file transfer protocols**: Utilize SFTP, HTTPS, or E2EE to ensure secure data transfer and storage.
- Verify end-point security**: Ensure that all endpoints, including devices and networks, have up-to-date security measures in place.
- Regularly update and patch software**: Keep software and systems up-to-date to prevent exploitation of vulnerabilities.
- Train employees**: Educate employees on secure data transfer best practices and the importance of secure data handling.
Conclusion
Secure online data transfer is a critical component of business continuity and data protection. By understanding the best secure online data transfer methods, tools, and protocols, organizations can effectively safeguard sensitive information from cyber threats. Remember to follow best practices, such as choosing secure file transfer protocols, verifying end-point security, and regularly updating software, to ensure that your organization's data remains secure and protected.