Protecting against Advanced Persistent Threats
Advanced Persistent Threats (APTs) are sophisticated, long-term cyberattacks that target sensitive data and resources. These threats are often launched by well-resourced and highly skilled attackers, making them difficult to detect and mitigate. To protect against APTs, organizations must adopt a multi-layered approach that integrates robust technologies, strong processes, and informed personnel.
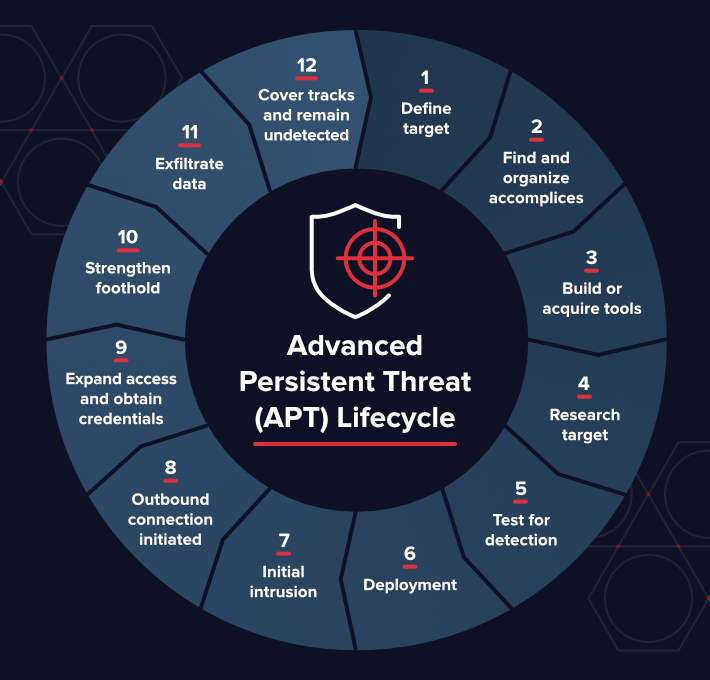
Understanding APTs
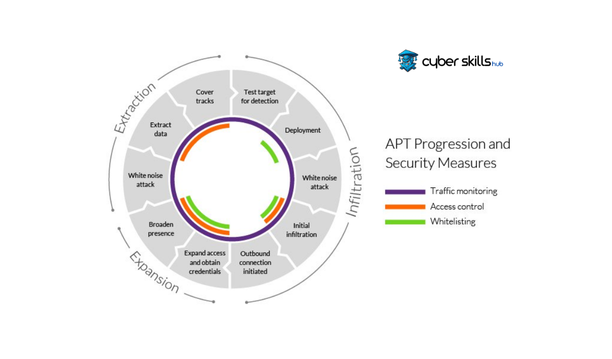
APTs are highly sophisticated attacks that involve multiple stages and techniques to evade detection and maintain control over compromised networks. These threats often involve lateral movement, privilege escalation, and persistence mechanisms to stay hidden in a system for an extended period. APTs can be challenging to identify and treat, due to their sophisticated tactics and targeted approach.
Key Strategies to Defend Against APTs
- Layered Defenses: A multi-layered approach to security is the most effective defense against APTs. This includes regular security assessments, ongoing employee cybersecurity training, continuous network monitoring, and the use of advanced threat detection technologies.
- Behavioral Detection: Behavioral detection mechanisms can help identify and block APTs by analyzing system behavior and detecting anomalies.
- Endpoint Security: Endpoint security solutions can help prevent APTs by blocking known and unknown threats, as well as detecting and responding to incidents.
- Network Segmentation: Network segmentation can help prevent APTs by isolating critical systems and data from the rest of the network.
- Incident Response: Having an incident response plan in place can help organizations quickly respond to and contain APTs.
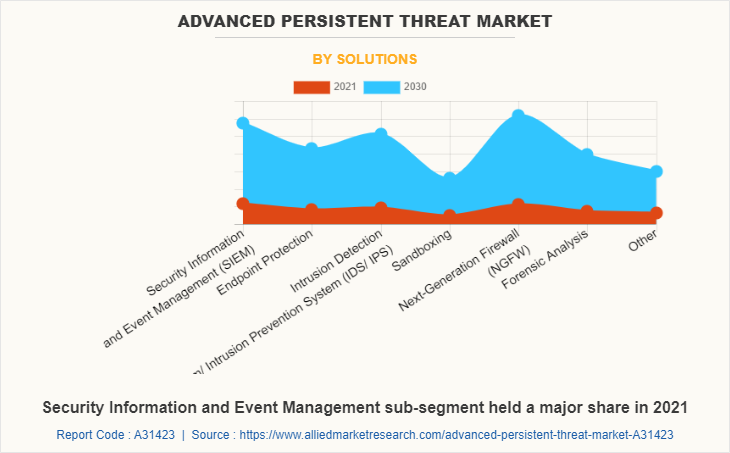
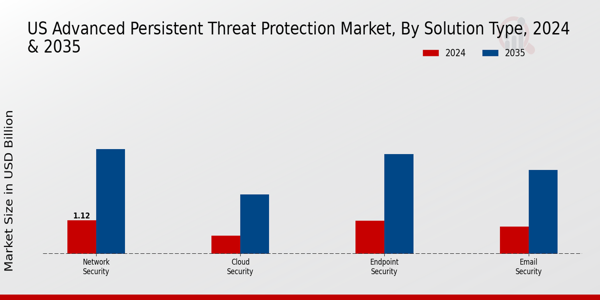
Technologies to Enhance APT Security
Several technologies can enhance an organization's overall security posture and make it more resilient against APTs. These include:

- Advanced Threat Detection: Solutions that use machine learning and other advanced techniques to detect and block APTs.
- Endpoint Detection and Response: Solutions that detect and respond to endpoint threats in real-time.
- Network Traffic Analysis: Solutions that analyze network traffic to detect and block APTs.
- Cloud Security: Solutions that provide cloud-based security and monitoring to detect and respond to APTs.
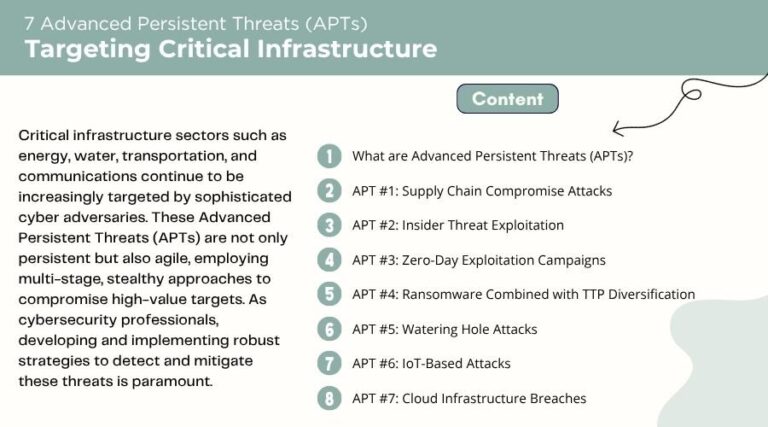
Real-World Examples of APTs
There have been several notable APT incidents in recent years, including:
- Operation Turla: A sophisticated APT campaign that targeted government and military organizations.
- Operation Elgin: A highly sophisticated APT campaign that targeted organizations in the defense and aerospace industries.
Conclusion
Protecting against APTs requires a comprehensive strategy that integrates robust technologies, strong processes, and informed personnel. By understanding APTs, implementing key strategies to defend against them, and using advanced technologies to enhance security posture, organizations can reduce the risk of APTs and protect sensitive data and resources.